Software supply chain attacks are going to be forever on the minds of CISOs and DevSecOps teams as commercial and public sector enterprises look for ways to avoid the headlines as the next SolarWinds.
Now’s the time for technology, collaboration, and compliance processes to come together to help protect software supply chains. Here are seven trends that paint a future picture of how it may all work:
1. Compliance Strengthens in the Face of Supply Chain Security
We’ve yet to see a full response from the compliance world — HIPAA, Sarbanes Oxley (SOX), and PCI-DSS — in the aftermath of the SolarWinds compromise. Responses from the compliance community are certain to come out as healthcare, financial services, and other compliance-governed industries seek advice and counsel about what makes for a compliant software supply chain to their auditors.
One compliance standard built for multi-vendor environments is the United States Government’s Federal Risk and Authorization Management Program (FedRAMP). When you peel away the bureaucracy and the politics, the federal government is just one big compliance play. They have the experience of integrating multiple vendors from large systems integrators, taking small to midsize companies into their software supply chain while maintaining security and compliance. However, despite all the goodness of FedRAMP, there’s little adoption outside of businesses that do government work.
2. Defense in Depth Protects the Software Supply Chain
Defense in Depth is a strategy where you treat every piece of software that you bring into your software supply chain as malicious actors regardless of whether the source where it’s your own developers, external suppliers, or open source. You run and monitor the software accordingly.
However, Defense-in-Depth is extremely expensive to do for real.
3. The Rise of Code as an Attack Vector
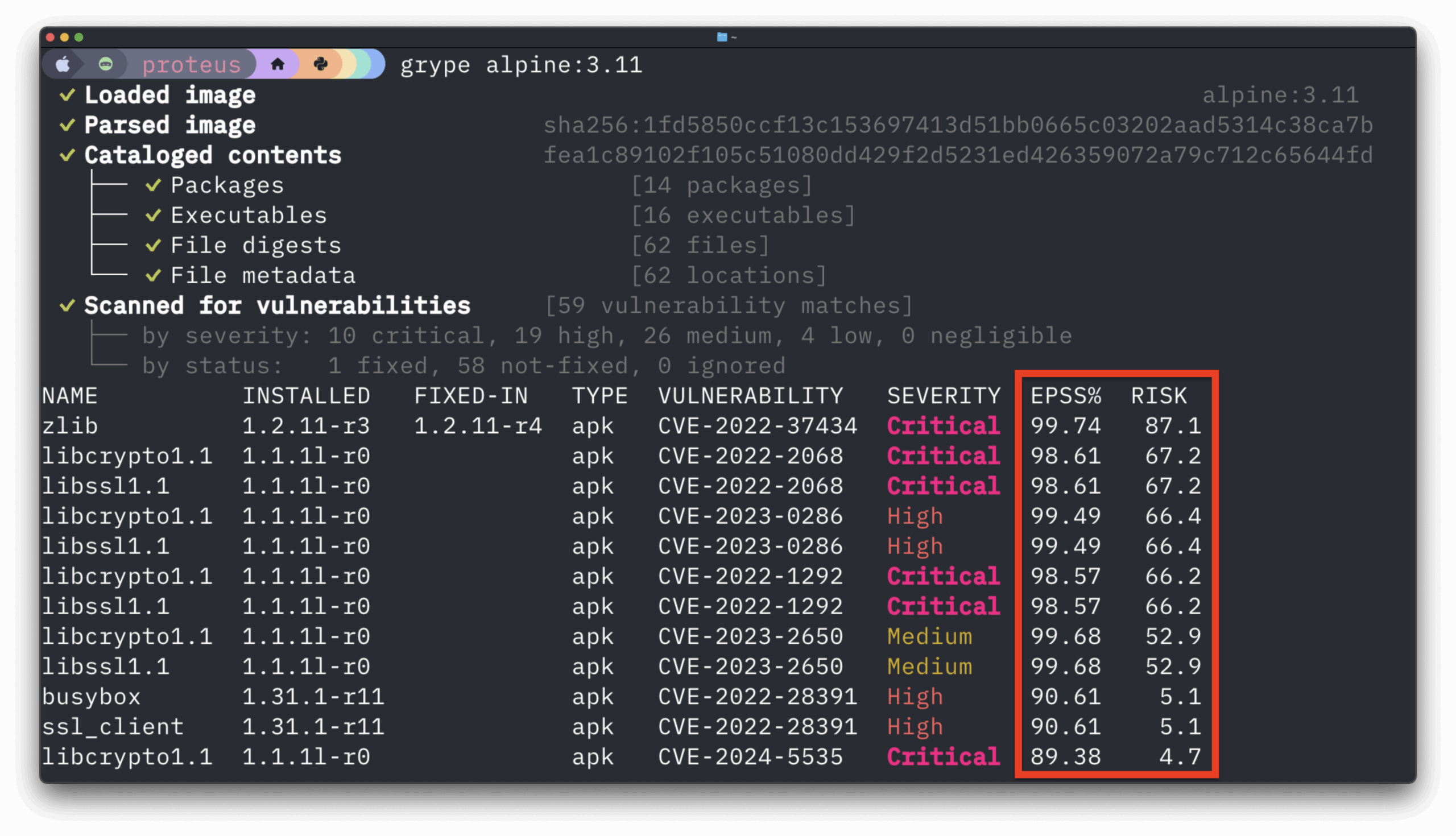
A software supply chain attack, such as we saw with SolarWinds, will put a renewed focus on code as an attack vector. DevSecOps, with the “shift left” culture it brings, will increasingly become a necessity for development teams up and down the software supply chain. Part of the shift-left culture is to equip your developers with lightweight tools to use locally to scan their code.
You can expect to see other mitigation strategies on the rise such as developing a robust code composition strategy with a detailed software bill of materials (SBOMs). Such strategies with a fully documented and verified change of custody for all software code entering the supply chain. Your developers can also run a secrets calling tool on all code repositories and include active monitoring. You should also have your developers or in-house cybersecurity team search for your code in public Git repositories, especially GitHub and GitLab. Finding your code once means there’s bound to be more of it out there.
Another strategy is to invest in tools to monitor code integrity and git misconfiguration. Deploy these tools in your DevSecOps pipelines and ensure that your supply partners are using the same or similar tools in their DevSecOps toolchains.
4. OSS and the Future of Supply Chain Security
There are bound to be more questions than ever about open source software (OSS) in enterprise software supply chains across industries and governments. While OSS is a foundation to leading DevOps, DevSecOps, and cloud-first initiatives, it will not stop technical and business leaders from asking even more questions about sourcing this critical software.
There are still more questions than answers about what the post-SolarWinds world may look like for major OSS projects prevalent in the enterprise. It may lend even more credence to the Red Hat business model and perhaps breed more companies taking ownership over some more facets of OSS.
Some in the OSS community are calling for more corporate open source citizenship. For-profit companies and even government agencies donate money, time, and expertise back to the OSS projects they use most to improve the project’s code security.
On the security front, it could mean that enterprises depending on OSS enlist mandatory code scanning tools to vet all the open source code entering the toolchain. It could lead to an onboarding process for open source code.
5. DevSecOps for Everybody!
DevSecOps could become one cost of entry for partners in a software supply chain soon. While criticisms about the validity of DevSecOps abound in some technology industry circles, the current situation offers the DevSecOps movement a time to prove itself. The benefits of well-executed DevSecOps across software supply chain providers include:
- A common language for developers, security, and operations teams
- Improved access to actionable data from backend development, build, and QA systems for reporting to stakeholders and auditors
- A development model that relates well to iterative software development and automated security testing at each phase of the development cycle
In the future, larger enterprises may demand contractually that all their suppliers follow a DevOps/DevSecOps model of development. However, such standardization of practices could be difficult, if not impossible, to enforce in all reality. However, startups already standardized on agile and DevOps gain a leg up if they have salespeople who can bring home large enterprise accounts.
6. Transparency Grows in the Software Supply Chain
DevOps and DevSecOps have driven home the need for transparency in the development lifecycle. Transparency needs to grow throughout the software supply chain during 2021 and beyond. One solution to make that happen is in-toto — a software supply chain security framework– that includes current integrations with Git, Docker, Datadog, and some other open source build tools.
7. Zero Trust across the Supply Chain
As concerns over software supply chain security grow in 2021 and beyond, zero trust security solutions may come to bear in the next generation of software supply chain security. However, there are some caveats to this approach. Zero trust security is still an emerging category (albeit with great potential). My colleague, Andre Neufville, wrote about how zero trust security can protect containers. It’s a technology bound to find itself in the software supply chain of the future because it treats all code as equally malicious while giving developers and security teams the tools and processes to help mitigate the associated risks.
Final Thoughts
There’s no denying that software supply chain security will forever remain a challenge. Given that, it doesn’t mean that your organization can’t be forward-thinking in the technologies and strategies that you put in place to mitigate risks across your software supply chain