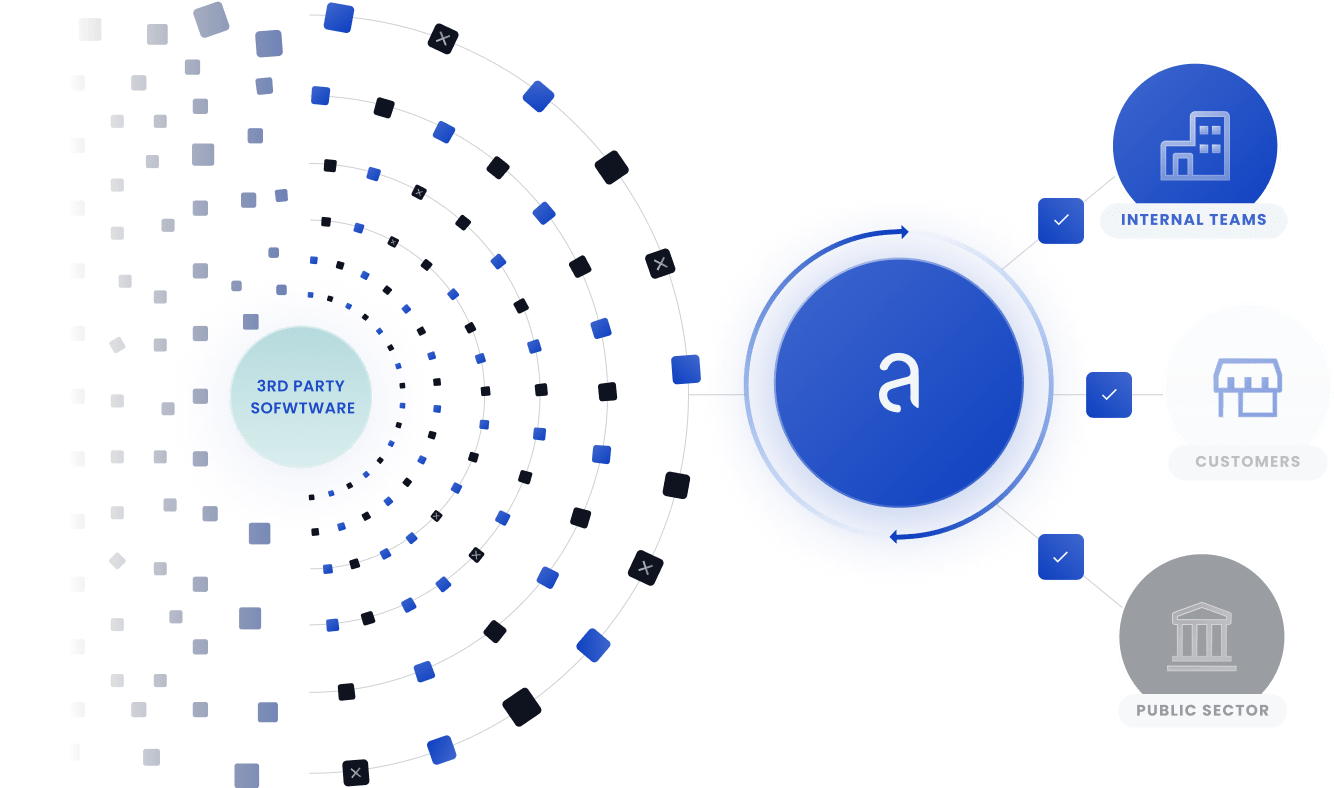
For Enterprises
Secure your software supply chain with confidence.
Continuous end-to-end security for your containerized applications.

Strengthen your brand by securing your process.
Source
Validate the security of direct and transitive open source dependencies and third-party containers.
Develop
Reduce time spent on rework by uncovering all your dependencies and security issues early.
Build
Lower remediation costs by continuously scanning for vulnerabilities, malware, cryptominers, and secrets in your CI/CD pipeline.
Stage
Assess complete applications for security vulnerabilities, compliance risks, and new dependencies.
Deploy
Prevent insecure apps from being deployed into production with policy controls and gates.
Run
Re-analyze SBOMs for released software to identify the impact of new vulnerabilities that arise post-deployment.
The Anchore Difference
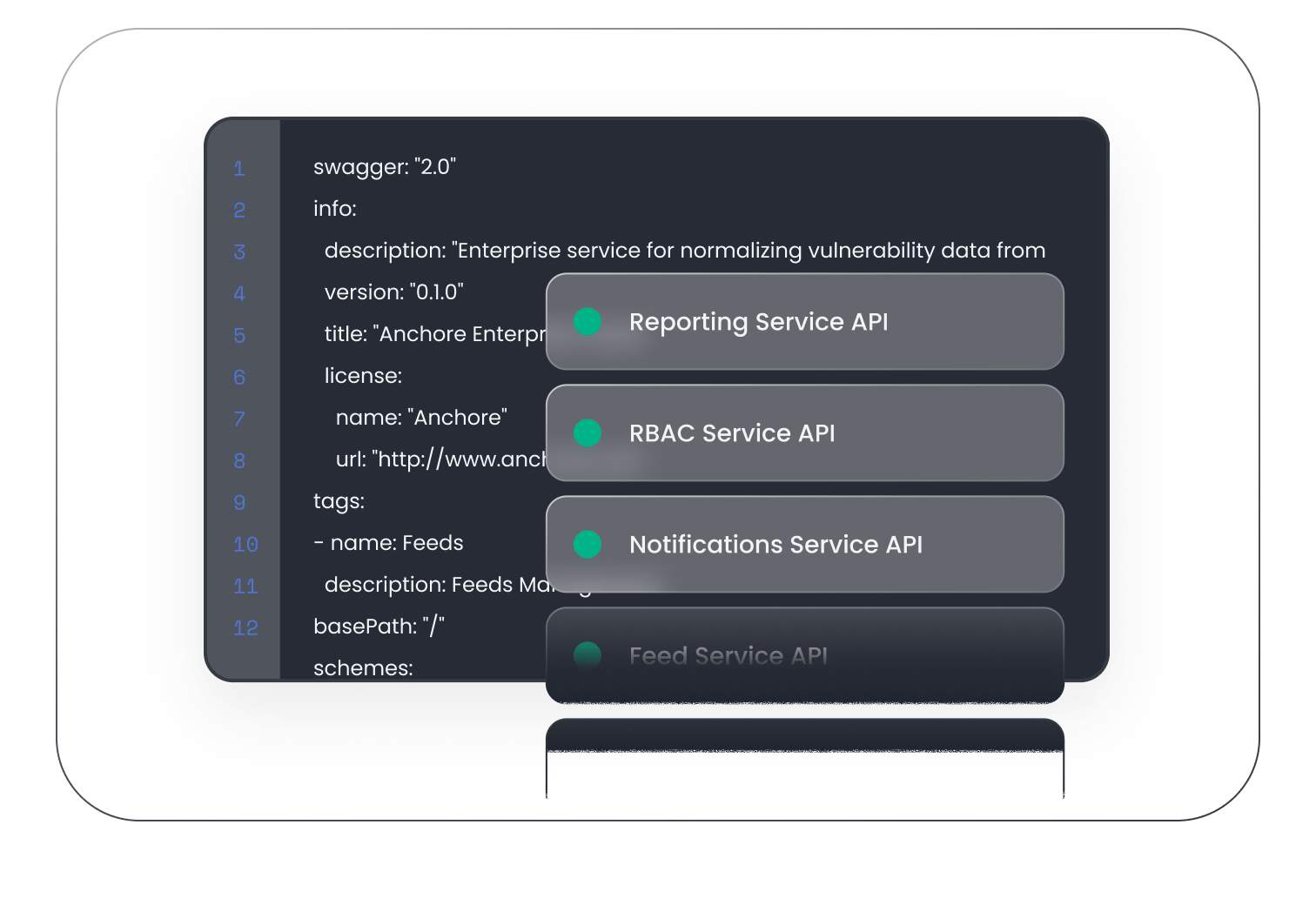
100% API coverage.
Easily integrate with the most popular development tools and achieve complete automation through fully documented APIs.
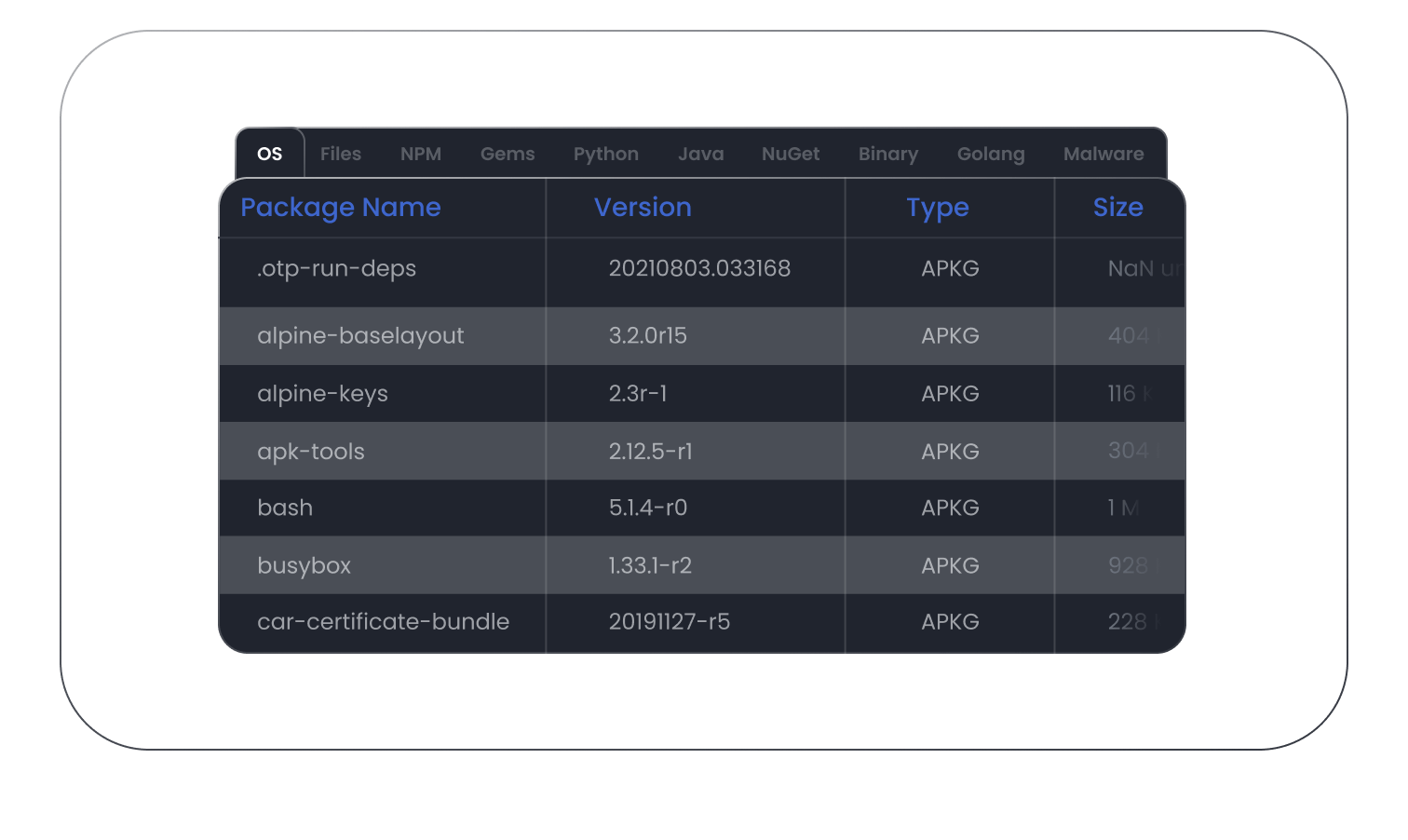
Powerful SBOM management.
Generate comprehensive SBOMs for your code repos and container images down to the file level. Track SBOMs for all your product releases to monitor security and share SBOMs to meet customer requirements.
Fewer false positives.
Accelerate software delivery with multiple vulnerability feeds, optimized vulnerability matching, allowlists, and a unique feedback loop that combine to reduce false positives.
Key capabilities.
End-to-End SBOM Management
Automatically generate comprehensive SBOMs at each step in the development lifecycle and store them in a repository for use in monitoring for new vulnerabilities and risks — even post-deployment.
Open Source Dependency Tracking
Use SBOMs to scan throughout the development cycle for both direct and transitive dependencies to pinpoint relevant open source vulnerabilities and to enforce policy rules.
Vulnerability Scanning & False Positive Management
Scan images for malicious code and secrets in development environments, CI/CD pipelines, container registries, and runtime environments while reducing false positives and false negatives.
SBOM Drift Detection
Detect SBOM drift in the build process by setting policy rules that alert when components are added, changed, or removed to quickly identify new vulnerabilities, developer errors, and malicious efforts to infiltrate builds.
Application-Level View of Risk
Tag and group all artifacts associated with an application, release, or service so you can report on vulnerabilities at the application level and monitor each application release for new risks — including zero-day vulnerabilities.
Flexible Policies for Compliance
Enforce compliance with internal standards or with such directives as DISA STIG, NIST, FedRAMP, CIS Benchmarks, and more using pre-built policy packs or custom policy rules.
Notifications & Alerts
Use email, Slack, Jira, or GitHub to notify developers and security teams of policy violations, secrets, malware, and more so they can take corrective action.
Remediation Recommendations
Reduce time spent fixing vulnerabilities with remediation recommendations and automated workflows to resolve the issue.
Continuous Visibility & Monitoring
Manage Kubernetes clusters to identify containers that are unscanned or have new vulnerabilities.
Security Reports & Audits
See the big picture with flexible reporting and easy-to-use dashboards for security teams or consume data through an API.
Integrations
Leverage fully supported integrations with the tools you already use, including major CI/CD tools, container registries, and container platforms.
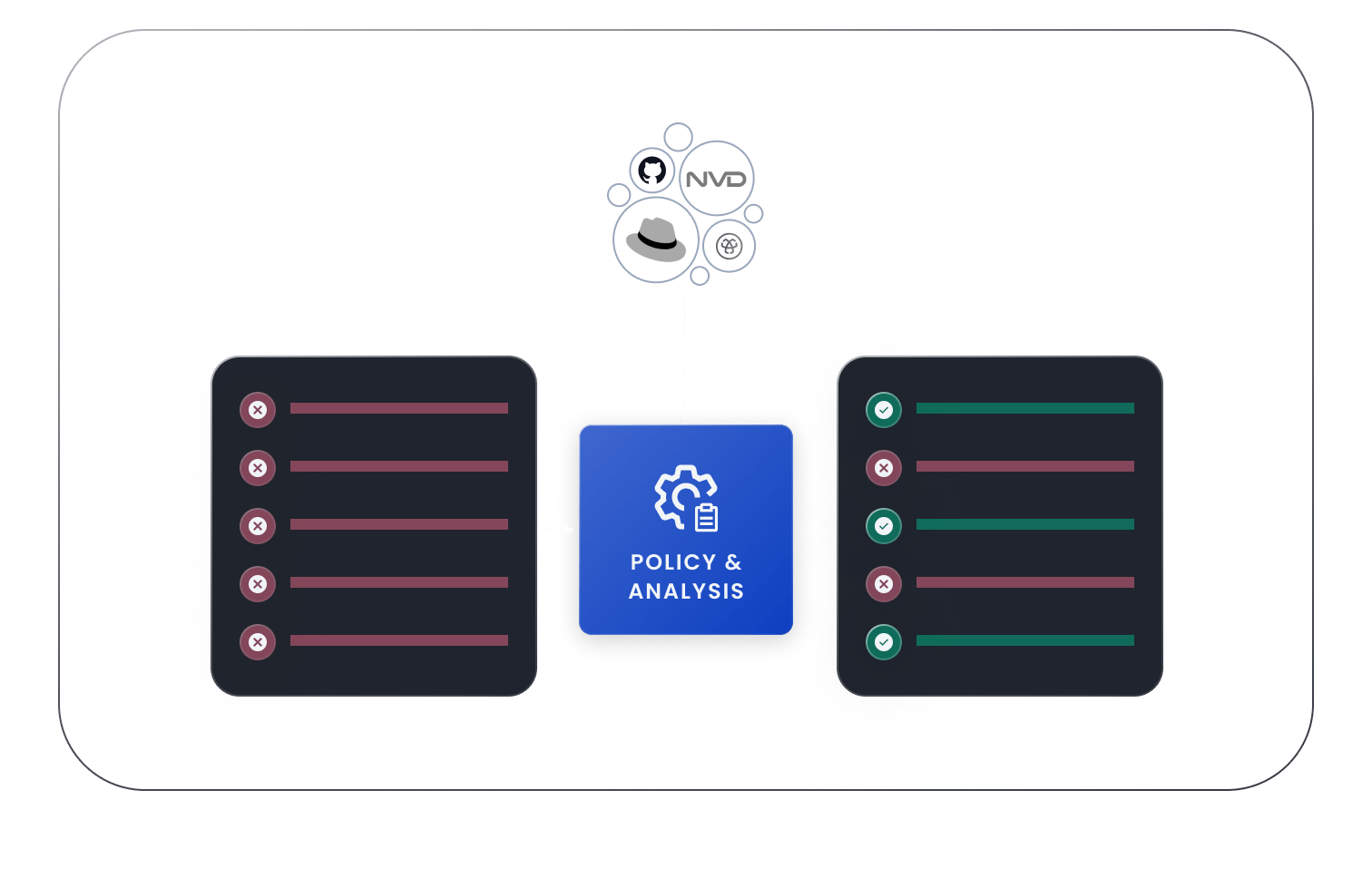
Enhanced Vulnerability Data
Access enhanced vulnerability data with a custom feed that curates data from multiple sources and enables optimized vulnerability matching.
Related resources.
Visually hidden 
Jun 14, 2021
The Fundamentals of Container Security
Download the White Paper
Visually hidden 

Dec 16, 2021
Understanding SBOM Management and The Six Ways It Prevents SBOM Sprawl
Read the Blog
Speak with our security experts
Learn how Anchore’s SBOM-powered platform can help secure your software supply chain.