Modern cloud-native software applications include software components and code from both internal developers and external sources such as open source communities or commercial software providers. Visibility into these components to identify vulnerabilities, security risks, misconfigurations, and bad practices is an integral part of securing the software supply chain. Anchore Enterprise 3.2 provides richer visibility into your software components so risks can be identified and quickly resolved.
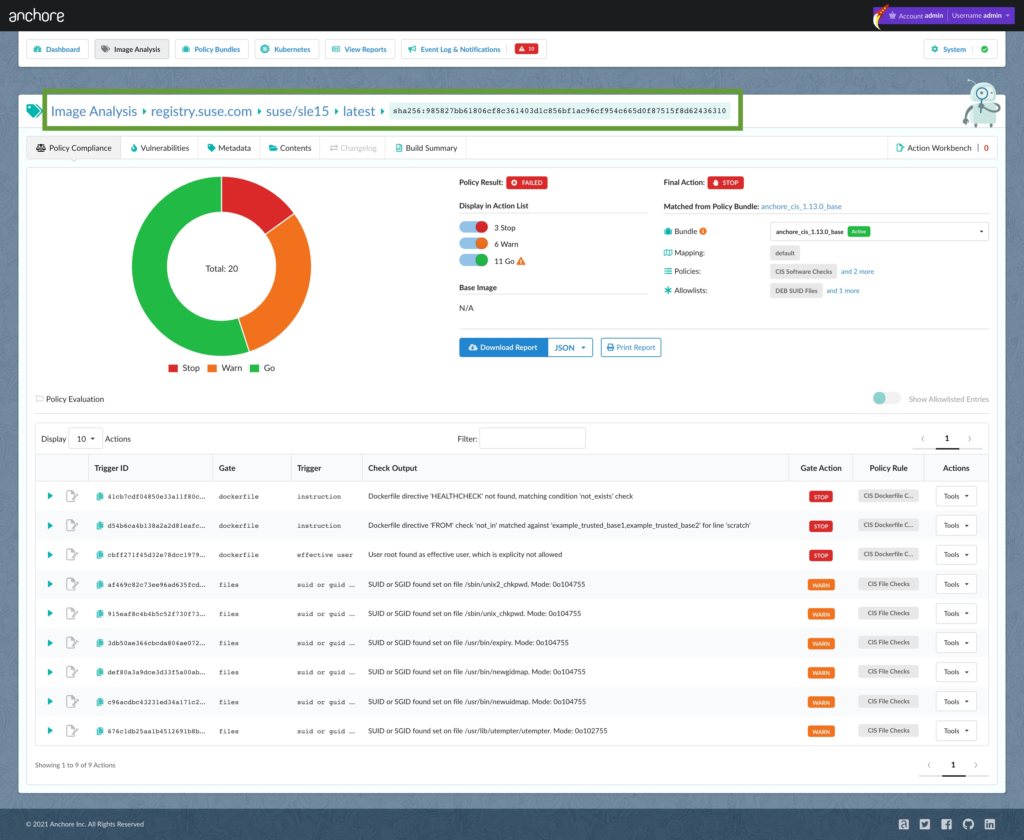
Discover and Mitigate Vulnerabilities and Security Risks Found in SUSE Enterprise Linux Containers
SUSE container image scan results
Anchore Enterprise 3.2 can now scan and continuously monitor SUSE container images for any security issues present in installed SUSE packages to improve their security posture and reduce threats. SUSE packages are now included in SBOMs as well as a comprehensive list of files. Additionally, customers can apply Anchore’s customizable policy enforcement to SUSE packages and vulnerabilities.
Identify Vulnerabilities More Accurately with Our Next-Generation Scanning Engine
Anchore Enterprise 3.2 now uses our next-generation scanning engine that builds upon capabilities in our open source tool Grype and also delivers more accurate results. Users will benefit from the fast pace of innovation while gaining all of the additional features that are available in Anchore Enterprise such as false-positive management. In addition, Grype users switching to Anchore Enterprise will benefit from consistent results between the two solutions, simplifying the transition. The 3.2 version of Anchore Enterprise provides richer visibility into your software components so risks can be identified and quickly resolved.
Note: Existing customers will need to select the next-generation engine in order to take advantage of these benefits. All new installations will default to the new scanning engine. For more information on how to switch, please see the release notes.
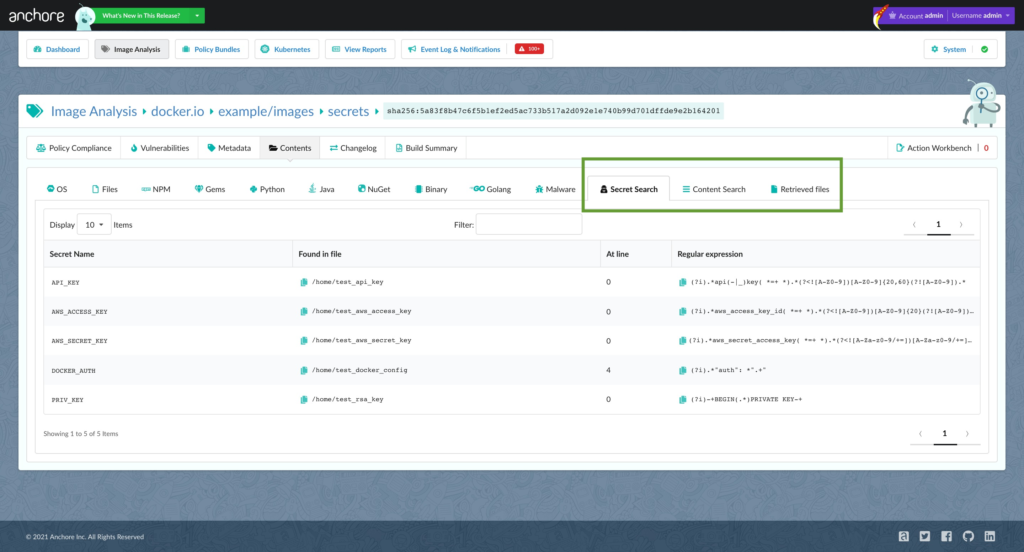
More Metadata Exposed in the UI for Policy Rules
New metadata tabs
Customers using Anchore Enterprise now have the ability to see additional SBOM file details in the UI that were previously available only through the API. This new UI visibility enables users to quickly and easily view data that can be instrumental in creating and tuning policy rules. The UI data additions include secrets for identifying credential information inadvertently included in container builds and file content checks which can be used for best practices such as making sure configurations are set correctly. The UI also now allows you to access retrieved files (files that you have designated to be saved during the scan) for further review and additional policy checks.
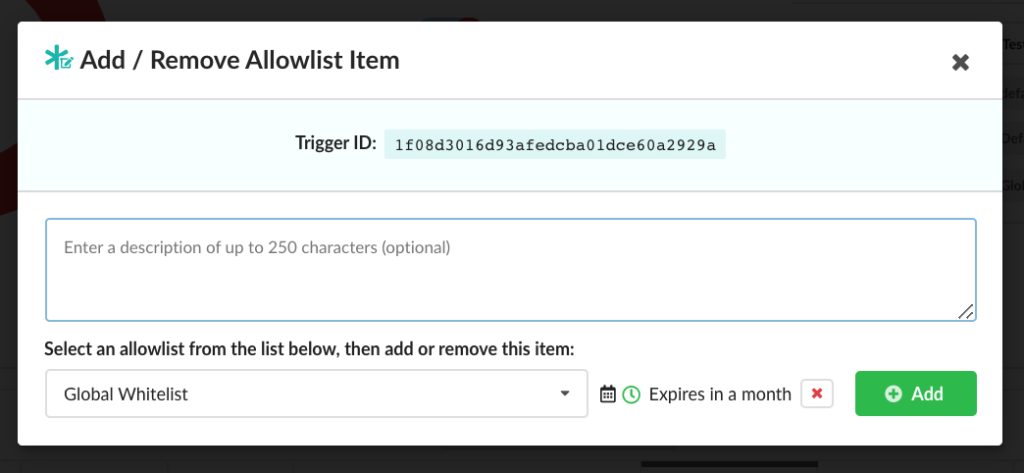
More Allowlist Customization Options in the UI
Allowlist customized by Trigger ID
Users now have additional Allowlist customization options in the UI. Allowlists enable development teams to continue working while issues are being investigated. Now in addition to vulnerabilities, users can add other policy checks to Allowlists through the UI which permits them to override specific policy violations for a more accurate final pass or fail recommendations on image scans.