It has been just a little over five months since Anchore opened its doors, and we’re happy to announce the General Availability of Anchore 1.0 - combining an open source platform for community participation while addressing enterprise needs through an on-prem offering with additional feature augmentation, and Anchore Navigator, anchore.com, a free service that provides an unparalleled level of visibility into the contents of container images.
As the adoption of containers continues to grow enterprises are increasingly demanding more visibility and control of their container environments. Today we see operations, security and compliance teams looking to add a level of governance to container deployments that were lacking during the early gold rush. The most common approach we have seen today is container image scanning which typically means scanning the operating system components of an image for security vulnerabilities, CVEs. While the need to scan an image for CVEs is undeniable it should only be the first step given the fact that each image typically contains hundreds of operating system packages, thousands of files along with application libraries and configuration files that are likely not part of the operating system image.
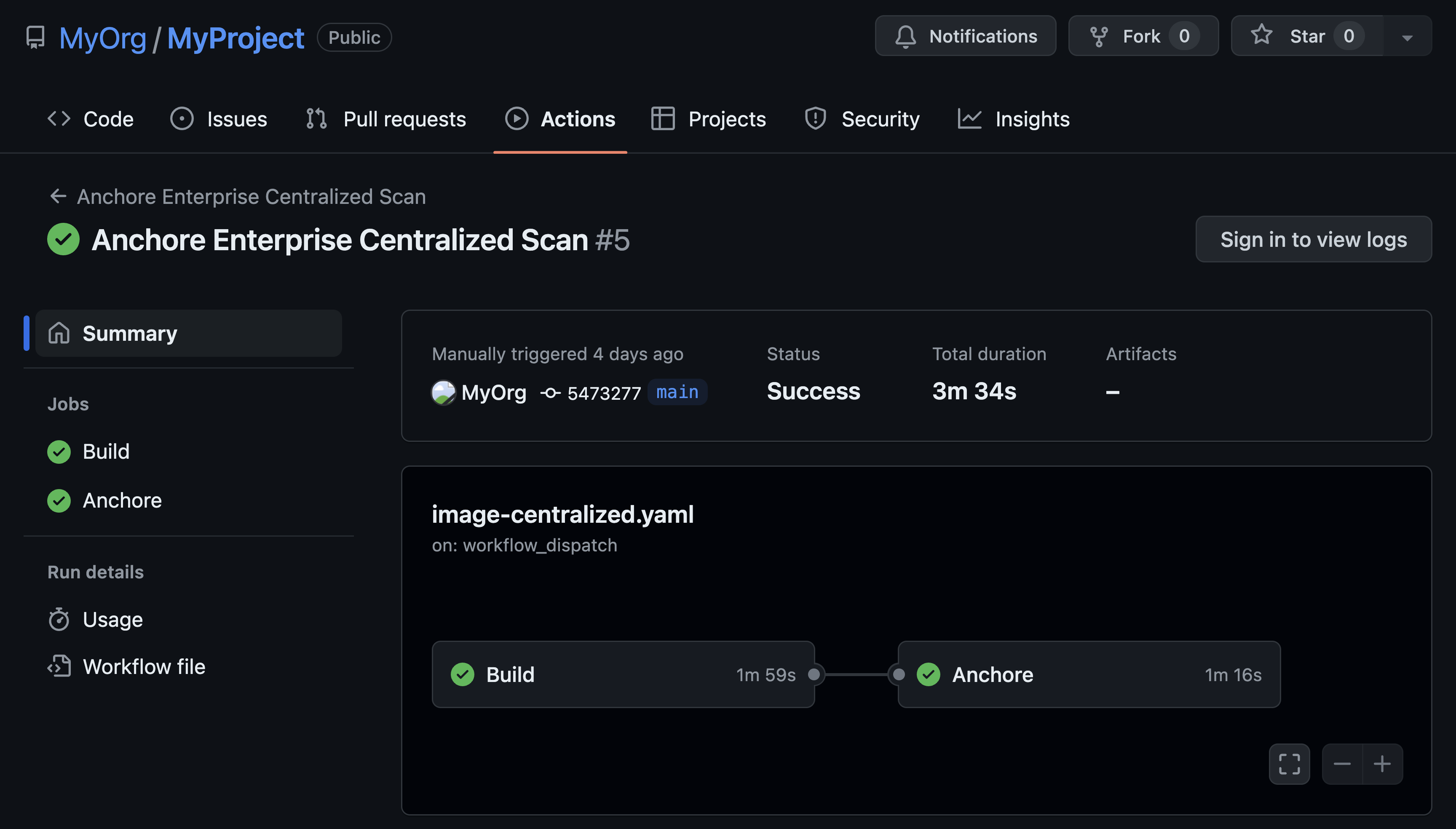
Anchore 1.0 was designed to address the lack of transparency, allowing developers, operations and security teams to get visibility into the entire contents of the containers - far more than the surface CVE scans that we have seen today. Empowered with this detailed information operations, security and compliance teams can define policies that govern the deployment of containers, including rules that cover security vulnerabilities, mandatory software packages, blacklisted software packages, required versions of software libraries, validated configuration files or any one of a hundred other tests that an enterprise may require to consider an image compliant.
The need for visibility and compliance extends beyond just point in time scanning of an image before deployment. In most cases application images are built from base images downloaded from public registries, these images may be updated often and in many cases without any obvious indication that a change was made let alone what was changed in these images. End-users have to struggle with the age-old choice: sticking with a known working but somewhat stale version, or use the latest, more feature-full, version and run the risk of security vulnerabilities, major bugs, and overall compliance deviation.
Full transparency is no longer just a good option to have in your toolset, but a mandate for application development and operations teams alike. Using the most stable and secure baseline of an IT service should no longer translate to an antiquated version of the software. With the fast pace of innovation also comes risk, and companies, big and small, will benefit greatly from simply and easily uncovering and tracking all changes throughout the application development and production lifecycle.