Anchore Enterprise
Software Composition Analysis for Cloud-Native Applications
Anchore is an SBOM-powered solution that enables continuous scanning of cloud applications for security and compliance issues.

THE ANCHORE PLATFORM
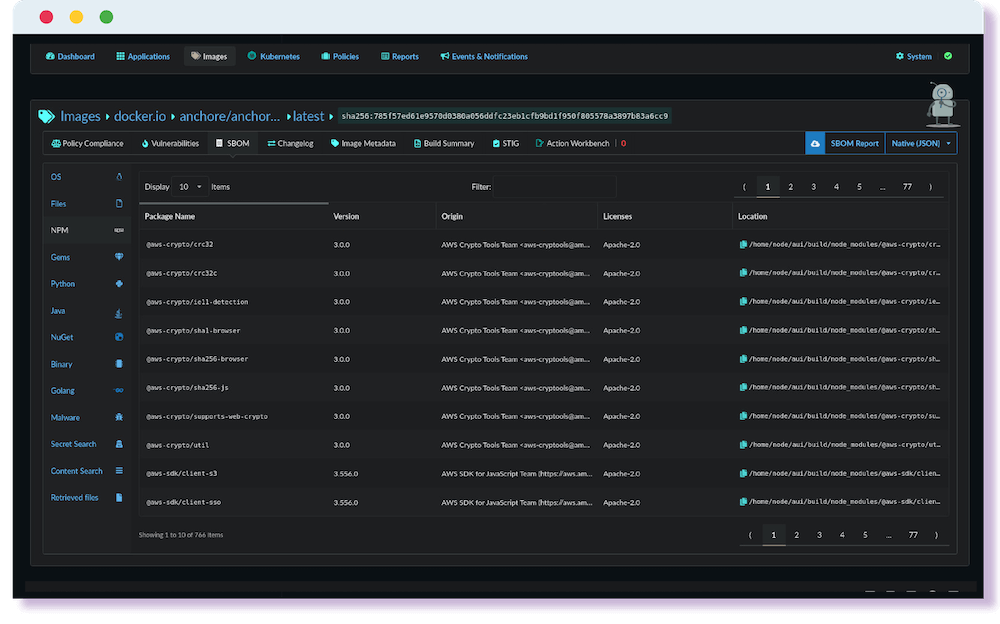
Powerful SBOM generation and management
Generate comprehensive SBOMs at every commit, every build, and every deployment. Capture dependencies, file metadata, licenses, and even content across your source code and containers.
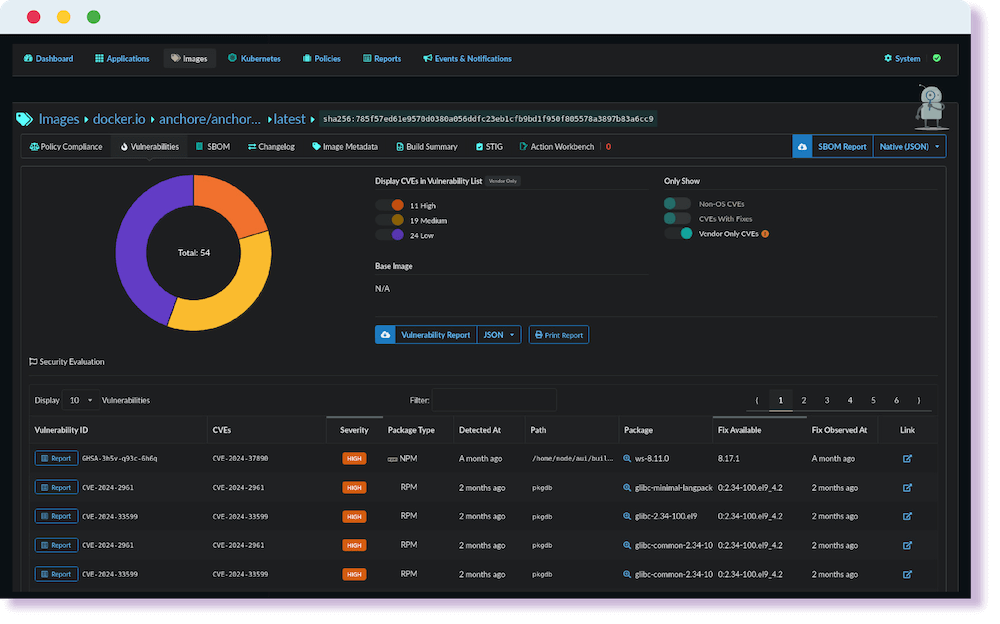
Continuous scanning of security issues
Continuously scan your SBOMs for vulnerabilities, secrets, and malware. Respond to active exploits or investigate historical risk.
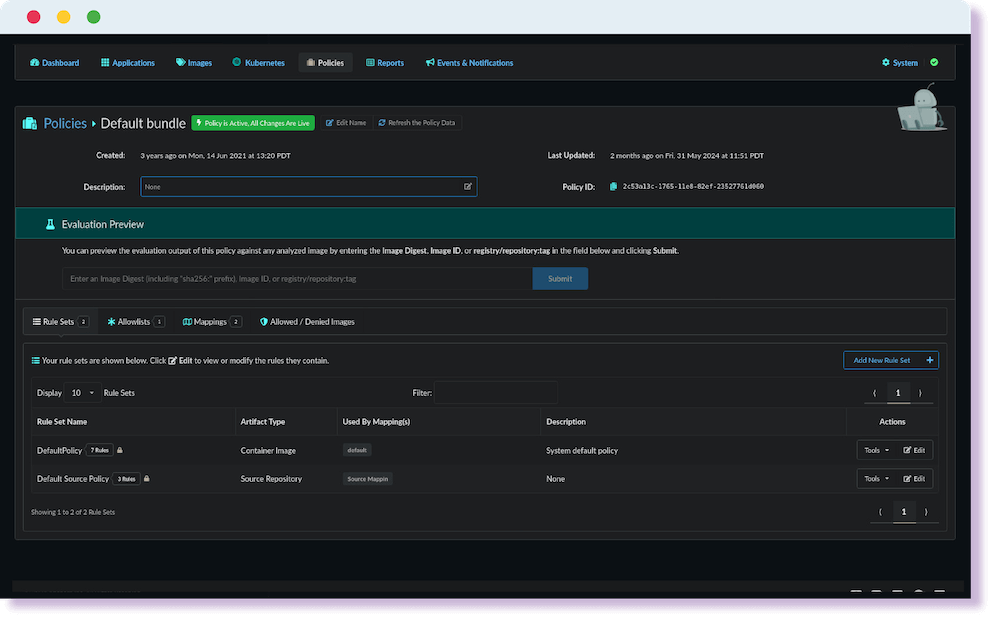
Automated compliance enforcement
Add compliance checks to your build pipelines and ensure your runtime environment meets formal requirements.
Key Features:
Container and Source Code SBOMs
Automatically generate SBOMs in your build pipeline or from artifact registries . Upload or download SBOMs in native Syft format, CyloneDX, or SPDX.
Cloud Runtime Inventory
Generate a list of running images in production across your EKS, ECS, AKE, GKE, or OpenShift cluster to prioritize triage and compliance workflows.
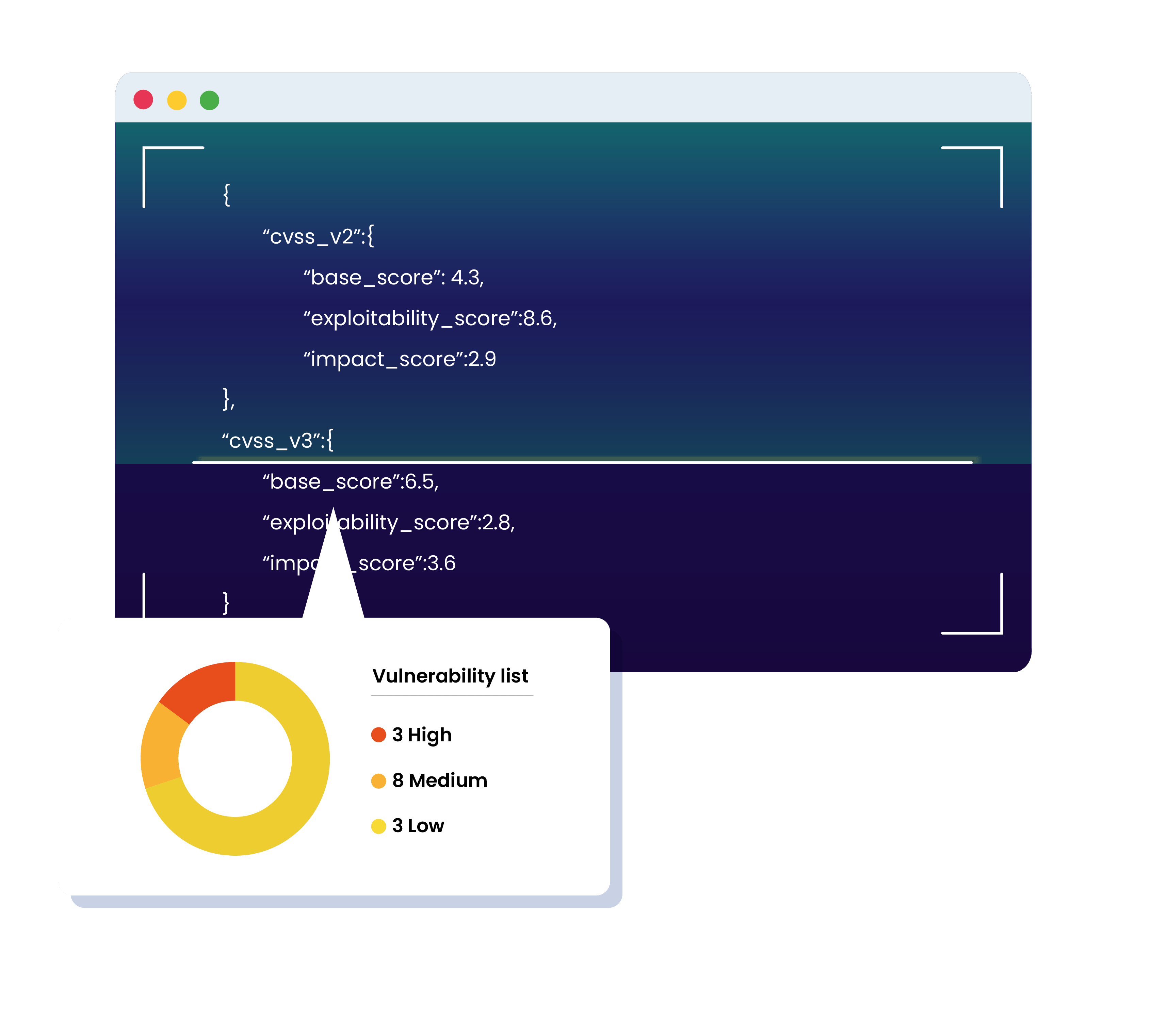
Continuous Vulnerability Scanning
Anchore’s SBOM-powered approach enables continuously scanning for new vulnerabilities instantly without needing access to the original software artifacts. Respond to 0-day events instantly or review historical risk.
Malware Scanning
Search for malware signatures in container images and block deployment to production in your build pipeline.
Secret Scanning
Identity unencrypted secrets based on common or user-defined regular expression patterns within any file in your image.
Compliance Policy Packs
Become NIST, FedRAMP, or DISA compliant quickly with ready to use policies that map to explicit controls. Shift compliance “left” by checking for compliance before software goes into production.
Policy as Code
Enforce internal best practices or formal compliance requirements in simple JSON instructions that can be version controlled in GIT.
License Checks
Block the use of unapproved licenses or search for licenses in response to audit requests.
Alerts
Send security or compliance finding alerts to developers in their native tooling to kickstart the remediation process.
Reporting
Create detailed, custom reports for security teams to assess impact and trends to help direct remediation efforts. Send auditors evidence of checks being performed and pass/fail status against formal controls.
API
Every feature and operation in Anchore can be instrumented using an API call. Create a 100% automated and integrated ‘headless’ solution with flexibility to define your preferred security workflow.
IL4-6 Ready
Anchore can be deployed in an air-gapped environment for use in classified or restricted access environments.
Easily integrates across your ecosystem























Trusted by Government and Fortune 500 companies for 8+ years.
Speak with our security experts
Learn how Anchore’s SBOM-powered platform can help secure your software supply chain.