The Cyber Maturity Model Certification (CMMC) is an important program to harden the cybersecurity posture of the defense industrial base. Its purpose is to validate that appropriate safeguards are in place to protect controlled unclassified information (CUI). Many of the organizations that are required to comply with CMMC are Anchore customers. They have the responsibility to protect the sensitive, but not classified data, of US military and government agencies as they support the various missions of the United States.
CMMC 2.0 Levels
- Level 1 Foundation: Safeguard federal contract information (FCI); not critical to national security.
- Level 2 Advanced: This maps directly to NIST Special Publication (SP) 800-171. Its primary goal is to ensure that government contractors are properly protecting controlled unclassified information (CUI).
- Level 3 Expert: This maps directly to NIST Special Publication (SP) 800-172. Its primary goal is to go beyond the base-level security requirements defined in NIST 800-171. NIST 800-172 provides security requirements that specifically defend against advanced persistent threats (APTs).
This is of critical importance as these organizations leverage common place DevOps tooling to build their software. Additionally, these large organizations may be working with smaller subcontractors or suppliers who are building software in tandem or partnership.
For example, a mega-defense contractor is working alongside a small mom-and-pop shop to develop software for a classified government system. Lots of questions we should have here:
- How can my company as a mega-defense contractor validate what software built by my partner is not using blacklisted software packages?
- How can my company validate software supplied to me is free of malware?
- How can I validate that the software supplied to me is in compliance with licensing standards and vulnerability compliance thresholds of my security team?
- How do I validate that the software I’m supplying is compliant not only against NIST 800-171 and CMMC, but against the compliance standards of my government end user (Such as NIST 800-53 or NIST 800-161)?
Validating Security between DevSecOps Pipelines and Software Supply Chain
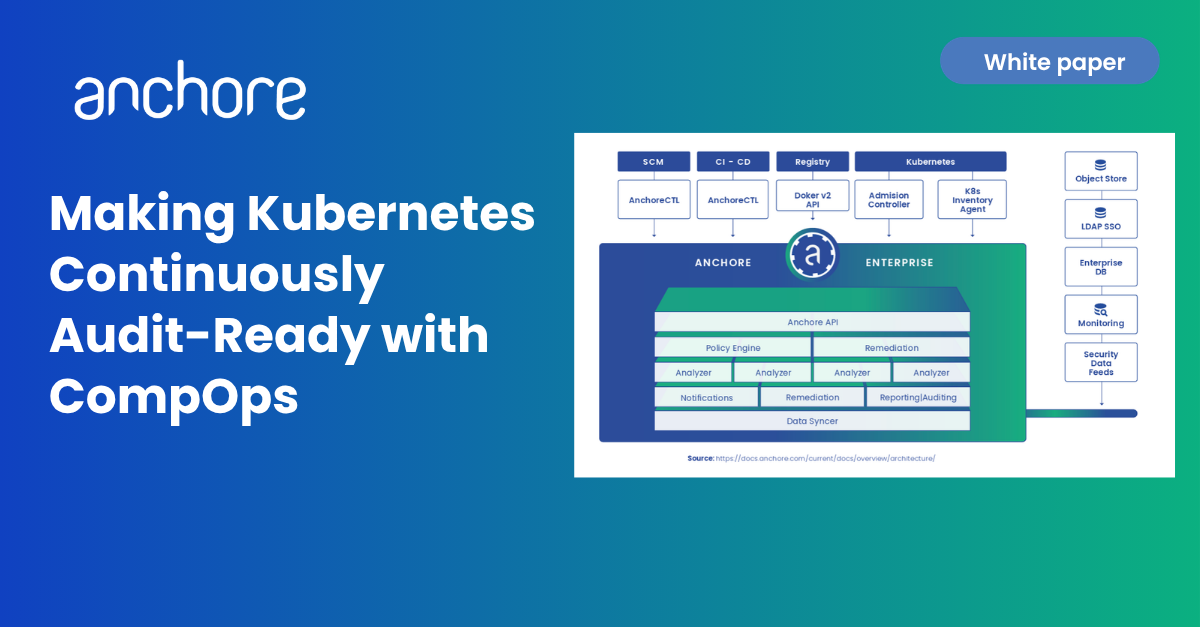
At any major or small contractor alike, everyone has taken steps to build internal DevSecOps (DSO) pipelines. However, the defense industrial base (DIB) commonly involves daily relationships in which smaller defense contractors supply software to a larger defense contractor for a program or DSO pipeline that consumes and implements that software. With Anchore Enterprise, we can now validate if that software supplied is compliant with CMMC controls as specified in NIST 800-171.
Looking to learn more about how to achieve CMMC Level 2 or NIST 800-171 compliance? One of the most popular technology shortcuts is to utilize a DoD software factory. Anchore has been helping organizations and agencies put the Sec in DevSecOps by securing traditional software factories, transforming them into DoD software factories.
Which Controls does Anchore Enterprise Automate?
3.1.7 – Restrict Non-Privileged Users and Log Privileged Actions
Related NIST 800-53 Controls: AC-6 (10)
Description: Prevent non-privileged users from executing privileged functions and capture the execution of such functions in audit logs.
Implementation: Anchore Enterprise can scan the container manifests to determine if the user is being given root privileges and implement an automated policy to prevent build containers from entering a runtime environment. This prevents a scenario where any privileged functions can be utilized in a runtime environment.
3.4.1 – Maintain Baseline Configurations & Inventories
Related NIST 800-53 Controls: CM-2(1), CM-8(1), CM-6
Description: Establish and maintain baseline configurations and inventories of organizational systems (including hardware, software, firmware, and documentation) throughout the respective system development life cycles.
Implementation: Anchore Enterprise provides a centralized inventory of all containers and their associated manifests at each stage of the development pipeline. All manifests, images and containers are automatically added to the central tracking inventory so that a complete list of all artifacts of the build pipeline can be tracked at any moment in time.
3.4.2 – Enforce Security Configurations
Related NIST 800-53 Controls: CM-2 (1) & CM-8(1) & CM-6
Description: Establish and enforce security configuration settings for information technology products employed in organizational systems.
Implementation: Implementation: Anchore Enterprise scans all container manifest files for security configurations and publishes found vulnerabilities to a centralized database that can be used for monitoring, ad-hoc reporting, alerting and/or automated policy enforcement.
3.4.3 – Monitor and Log System Changes with Approval Process
Related NIST 800-53 Controls: CM-3
Description: Track, review, approve or disapprove, and log changes to organizational systems.
Implementation: Anchore Enterprise provides a centralized dashboard that tracks all changes to applications which makes scheduled reviews simple. It also provides an automated controller that can apply policy-based decision making to either automatically approve or reject changes to applications based on security rules.
3.4.4 – Run Security Analysis on All System Changes
Related NIST 800-53 Controls: CM-4
Description: Analyze the security impact of changes prior to implementation.
Implementation: Anchore Enterprise can scan changes to applications for security vulnerabilities during the build pipeline to determine the security impact of the changes.
3.4.6 – Apply Principle of Least Functionality
Related NIST 800-53 Controls: CM-7
Description: Employ the principle of least functionality by configuring organizational systems to provide only essential capabilities.
Implementation: Anchore Enterprise can scan all applications to ensure that they are uniformly applying the principle of least functionality to individual applications. If an application does not meet this standard then Anchore Enterprise can be configured to prevent an application from being deployed to a production environment.
3.4.7 – Limit Use of Nonessential Programs, Ports, and Services
Related NIST 800-53 Controls: CM-7(1), CM-7(2)
Description: Restrict, disable, or prevent the use of nonessential programs, functions, ports, protocols, and services.
Implementation: Anchore Enterprise can be configured as a gating agent that will scan for specific security violations and prevent these applications from being deployed until the violations are remediated.
3.4.8 – Implement Blacklisting and Whitelisting Software Policies
Related NIST 800-53 Controls: CM-7(4), CM-7(5)
Description: Apply deny-by-exception (blacklisting) policy to prevent the use of unauthorized software or deny-all, permit-by-exception (whitelisting) policy to allow the execution of authorized software.
Implementation: Anchore Enterprise can be configured as a gating agent that will apply a security policy to all scanned software. The policies can be configured in a black- or white-listing manner.
3.4.9 – Control and Monitor User-Installed Software
Related NIST 800-53 Controls: CM-11
Description: Control and monitor user-installed software.
Implementation: Anchore Enterprise scans all software in the development pipeline and records all user-installed software. The scans can be monitored in the provided dashboard. User-installed software can be controlled (allowed or denied) via the gating agent.
3.5.10 – Store and Transmit Only Cryptographically-Protected Passwords
Related NIST 800-53 Controls: IA-5(1)
Description: Store and transmit only cryptographically-protected of passwords.
Implementation: Anchore Enterprise can scan for plain-text secrets in build artifacts and prevent exposed secrets from being promoted to the next environment until the violation is remediated. This prevents unauthorized storage or transmission of unencrypted passwords or secrets. See screenshot below to see this protection in action.
3.11.2 – Scan for Vulnerabilities
Related NIST 800-53 Controls: RA-5, RA-5(5)
Description: Scan for vulnerabilities in organizational systems and applications periodically and when new vulnerabilities affecting those systems and applications are identified.
Implementation: Anchore Enterprise is designed to scan all systems and applications for vulnerabilities continuously and alert when any changes introduce new vulnerabilities. See screenshot below to see this protection in action.
3.11.3 – Remediate Vulnerabilities Respective to Risk Assessments
Related NIST 800-53 Controls: RA-5, RA-5(5)
Description: Remediate vulnerabilities in accordance with risk assessments.
Implementation: Anchore Enterprise can be tuned to allow or deny changes based on a risk scoring system.
3.12.2 – Implement Plans to Address System Vulnerabilities
Related NIST 800-53 Controls: CA-5
Description: Develop and implement plans of action designed to correct deficiencies and reduce or eliminate vulnerabilities in organizational systems.
Implementation: Anchore Enterprise automates the process of ensuring all software and systems are in compliance with the security policy of the organization.
3.13.4 – Block Unauthorized Information Transfer via Shared Resources
Related NIST 800-53 Controls: SC-4
Description: Prevent unauthorized and unintended information transfer via shared system resources.
Implementation: Anchore Enterprise can be configured as a gating agent that will scan for unauthorized and unintended information transfer and prevent violations from being transferred between shared system resources until the violations are remediated.
3.13.8 – Use Cryptography to Safeguard CUI During Transmission
Related NIST 800-53 Controls: SC-8
Description: Transmission Confidentiality and Integrity: Implement cryptographic mechanisms to prevent unauthorized disclosure of CUI during transmission unless otherwise protected by alternative physical safeguards.
Implementation: Anchore Enterprise can be configured as a gating agent that will scan for CUI and prevent violations of organization defined policies regarding CUI from being disclosed between systems.
3.14.5 – Periodically Scan Systems and Real-time Scan External Files
Related NIST 800-53 Controls: SI-2
Description: Perform periodic scans of organizational systems and real-time scans of files from external sources as files are downloaded, opened, or executed.
Implementation: Anchore Enterprise can be configured to scan all external dependencies that are built into software and provide information about relevant security vulnerabilities in the software development pipeline. See screenshot below to see this protection in action.
Wrap-Up
In a world increasingly defined by software solutions, the cybersecurity posture of defense-related industries stands paramount. The CMMC, a framework with its varying levels of compliance, underscores the commitment of the defense industrial base to fortify its cyber defenses.
As a multitude of organizations, ranging from the largest defense contractors to smaller mom-and-pop shops, work in tandem to support U.S. missions, the intricacies of maintaining cybersecurity standards grow. The questions posed exemplify the necessity to validate software integrity, especially in complex collaborations.
Anchore Enterprise solves these problems by automating software supply chain security best practices. It not only automates a myriad of crucial controls, ranging from user privilege restrictions to vulnerability scanning, but it also empowers organizations to meet and exceed the benchmarks set by CMMC and NIST.
In essence, as defense entities navigate the nuanced web of software development and partnerships, tools like Anchore Enterprise are indispensable in safeguarding the nation’s interests, ensuring the integrity of software supply chains, and championing the highest levels of cybersecurity.
If you’d like to learn more about the Anchore Enterprise platform or speak with a member of our team, feel free to book a time to speak with one of our specialists.