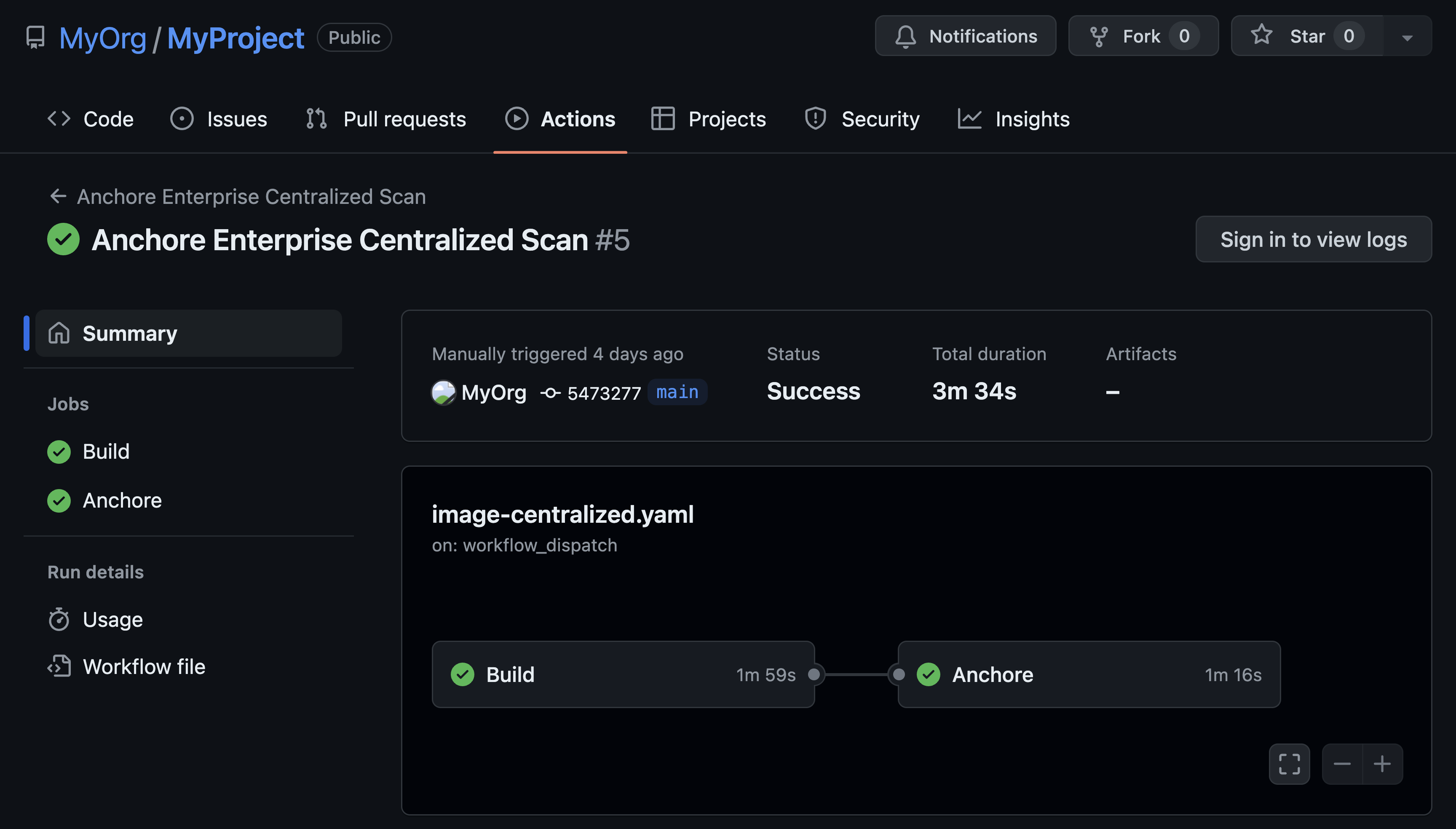
The ease of access a container registry provides users is a clear advantage over legacy code storage methods. However, just like almost any other type of technology, it has the potential to house and propagate malicious code. Docker Hub was a prime example of this, as is detailed in this post about malicious cryptocurrency mining code being buried in popular images. Any container registry is susceptible to this. Therefore, scanning images for vulnerabilities and malicious code is critical for organizational security and the security of the development community as a whole.
Reason 1 - Internal Company Security
To deliver a quality software product, companies need to ensure that the tools they use internally are secure and can be relied on. Auditing self-managed company registries is an important part of that process, especially if the code contained in those registries is written by external sources. It is easy for an engineer to accidentally introduce malicious code to the registry without knowing. By ensuring that tools are secure, the end product that is delivered to customers, as well as important, proprietary company information, can be kept secure.
Reason 2 - Product Security
Securing a product is an important consideration that all software companies must keep in mind when contemplating the methods they use to deliver code to their customers. Auditing registries that hold code available to customers is a way companies can ensure that any code delivered lives up to their security standards and that no vulnerabilities whether intentional or unintentional slip through the cracks. Additionally, certain industries have stringent guidelines that any software product must adhere to. An example is the healthcare industry. The importance of securing HIPAA protected data cannot be overstated, so checks to ensure that data leaks are not possible are important to maintaining compliance under government and company guidelines and requirements. This helps maintain trust with regulatory authorities and with customers.
Reason 3 - Open Source Security
Open source security is the third and perhaps most important reason to implement registry audits. Large open source registries have code flooding into them from anyone, anywhere, with any intention. It is all too easy for a person to create an image and push it to Docker Hub. A nefarious image disguised as a common open source project such as MySQL has the potential to wreak havoc on those who unwittingly deploy that image. By maintaining the integrity of the code that is available to the open source community, public registry maintainers can ensure that those who use the containers to build other products or learn are protected from attacks or attempts to steal their data.
The importance of container registry audits cannot be overstated. Containerization is an important development in the software delivery process. It has allowed for the quick and flexible deployment of countless applications, but it has taken the transparency to the user all but away making it difficult for a developer or user to know exactly what the code they are using is doing. With this loss of transparency, users, developers and anyone else who access these containers, needs to know that they are safe from malicious code and data security violations. By auditing the registries that secure that code, users can rest assured that the containers they use are safe and that the data they feed those containers is equally safe.