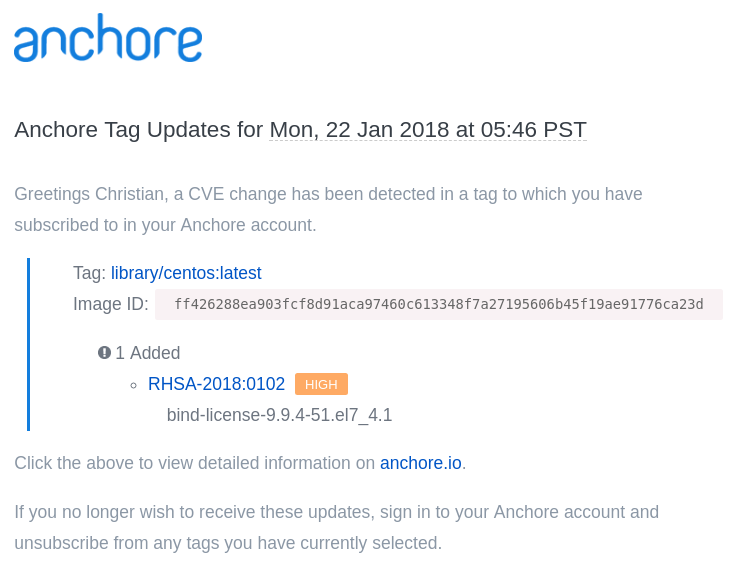
If like me you’re subscribed to receive updates for popular base images such as CentOS, then this morning you may have received an email like this from Anchore:
Here, you are receiving a warning that a new, HIGH severity CVE was just found in the CentOS image. You can read more about the vulnerability in Red Hat’s security advisory RHSA-2018:0102 which covers the impact of CVE-2017-3145 on the BIND DNS package.
As you can see from reading the advisory, an attacker could “potentially use this flaw to make named, acting as a DNSSEC validating resolver, exit unexpectedly … via a specially crafted DNS request.”
However the base CentOS image does not include the BIND DNS package, but it does include the bind-license package which contains a single text file container copyright information for BIND. While the security advisory lists all bind-* packages the copyright license file can obviously not be exploited by a specially crafted DNS request!
While this CVE can safely be ignored in the security vulnerability page for library/centos:latest or any images built from this base image it is likely that your policy checks will fail this image due to the High Severity vulnerability.
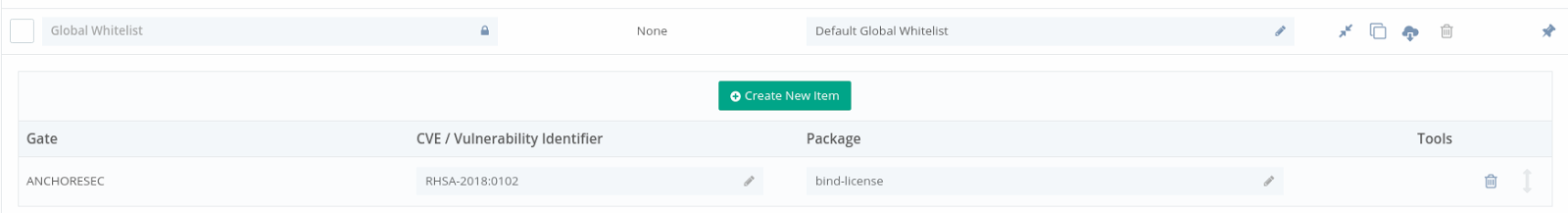
In my environment, I use the Global Whitelist feature for this very reason. It allows me to add an exception to ensure that the RHSA-2018:0102 vulnerability does not incorrectly block my CentOS or RHEL images.
In the screenshot below you can see that I have whitelisted RHSA-2018:0102 and in the package field I have specified the bind-license package to ensure that we only whitelist this package and not a binary package that is actually exploitable.
Using the free Anchore Cloud service you can receive notifications for image updates, paid subscribers receive policy and CVE updates such as the one covered by this blog.