Last week, President Biden released an executive order (EO) mandating a sweeping review of the federal government’s supply chains. In response to high-profile software supply chain hacks most notably the recent SolarWinds hack, the order went beyond physical supply chains to address the security of software supply chains as well.
The federal government depends on supply chains to provide material support for everything from personal protective equipment (PPE) for frontline workers to furniture for State Department facilities worldwide to complex IT systems across the DoD and civilian government agencies. Fortune 1000 corporation supply chains serve a similar role to companies and often stretch to suppliers around the world. The fact that this order makes direct mention of software supply chains is an indicator of the role software plays in our daily lives.
Treat this Executive Order as a Call to Action
The sheer complexity of software supply chain security means it’s time for commercial and public sector DevSecOps teams to learn from one another. The executive order makes the following request for a review of information technology software, data, and services that the government purchases with their 53.36 billion dollar IT budget.
"The Secretary of Commerce and the Secretary of Homeland Security, in consultation with the heads of appropriate agencies, shall submit a report on supply chains for critical sectors and subsectors of the information and communications technology (ICT) industrial base (as determined by the Secretary of Commerce and the Secretary of Homeland Security), including the industrial base for the development of ICT software, data, and associated services."
While this EO directly hits systems integrators (SIs) and other businesses that do work for the Department of Defense and civilian government agencies, the EO also applies to manufacturers in the semiconductor and other industrial bases that serve as foundations to the economic prosperity and security of the United States.
Key Considerations of Software Supply Chain Security
Every software supply chain security initiative in the aftermath of SolarWinds needs to encompass two major aspects. First, it must cover the security of the workloads or applications being constructed,and second, it must cover the security of the DevSecOps toolchain” (eg the tools, platforms and infrastructure) that is used to build the software. While cybersecurity teams have long focused on securing production infrastructure, the SolarWinds breach has called attention to the need to better secure the systems used by developers to build software applications.
Secure the Workload
Securing the software workload is a common practice that starts with setting policies to govern the use of source code from public repositories such as GitHub and ensuring software in your private repositories is properly vetted and secured. Policies should also extend to employees and contractors housing your source code in their personal source code repository accounts. Another crucial security step is to secure your source code “secrets” — application programming interface (API) keys, OAuth tokens, passwords, and more — that can provide authorized access to your application. Secrets that are left in source code are available to all repository contributors, whether cloned, copied, or distributed. If an attacker gains access to your source code repository, your secrets can be co-opted for their malicious attack.
Beyond the usual source code security concerns, there is also the prospect of intellectual property (IP) theft if an attacker accesses your source code repository. High-profile software source code leaks have struck both the consumer and defense industries for various reasons.
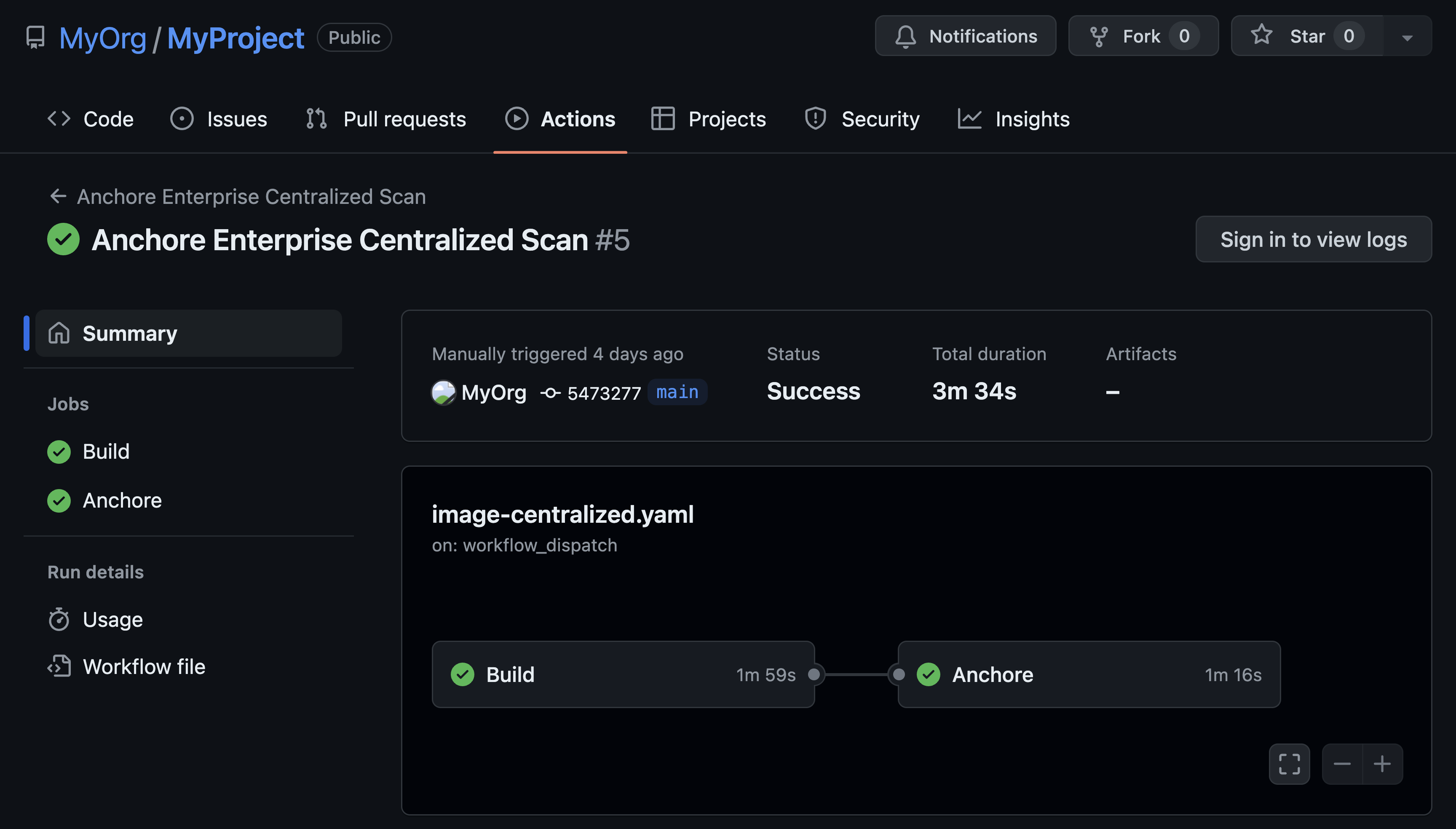
Because modern, cloud-native applications are often composed of a myriad of containers from open source and software suppliers, securing containers should take the form of a zero-trust strategy. Because containers may enter the software development process at many different points, organizations must embed continuous compliance and security checks at each stage of the development lifecycle. You can use open source or commercial tools to scan containers for vulnerabilities and generate a software bill of materials (SBOM) to ensure the software components match the vendor contract or documentation.
Secure the Toolchain
The next key security move is securing the entire software development toolchain -- the entire set of tools and platforms that are used to build your workloads.-. You should focus on the security of your DevSecOps toolchains including your continuous integration/continuous development (CI/CD) platforms. Such systems can become a target for man in the middle (MiTM) and other attacks. Security measures include:
- Protecting distributed applications
- Securing wired and wireless access points
- Mandating VPN access for remote workers
- Creating policies and controls to protect against unapproved shadow DevOps tools
Ensuring the security of your test/QA environments should be an integral part of your QA infrastructure build-out. It helps to have QA staff with a grounding in secure architecture to make this happen. If nobody on your QA team has that skill, look for ways to assign a member of your security or operations team to support the build-out of your QA infrastructure.
Security of production infrastructure is the area where most security teams already spend significant effort, including implementing threat detection, runtime application self-protection (RASP), and related measures. Expanding the security focus to include the systems used in earlier stages of the software development process provides additional layers of protection and improves the overall security of the software supply chain.
Take Action
Now is the time to reevaluate your software supply chain security. Here are some immediate steps to take:
- Audit your source code repositories especially access management and secrets security.
- Examine the feasibility of a zero-trust security strategy for your source code and work with your DevSecOps teams to create a roadmap/plan on how your organization can implement such a strategy to protect your source code.
- Implement tools to enable your DevSecOps team to generate an SBOM for open source and commercial software components you are onboarding to your toolchain.
- Audit your DevOps toolchain security and architecture if you haven’t already done so with an eye on protecting distributed applications, securing wired and wireless access points, mandating VPN access for remote workers, plus creating policies and controls to protect against Shadow DevOps tools.
- Audit the security of your Test/QA infrastructure, focusing on the architecture and then the same security elements as the rest of your DevOps toolchain security audit.
- Reinforce your application production security with threat detection, RASP, and other tools to shield your production applications from attackers.
Request a demo today to learn how Anchore Enterprise can help secure your DevOps toolchains and software supply chains!