In February 2020, the Linux Foundation released a report titled “Vulnerabilities in the Core,” a detailed analysis of the usage and security implications of open source software across the computing landscape. In today’s blog post, we will discuss some of the findings contained in the report, and explore how it pertains to the field of DevSecOps.
By now, the advantages of open source software are well understood throughout the industry. Software development teams can achieve faster delivery times and reduce costs by building on top of existing open source software components that are available for anyone to use. In the age of faster development cycles and continuous integration, it is often essential to incorporate open source technologies into the development stream in order to achieve and maintain the engineering velocity required for success.
However, the report demonstrates that open source software is not immune to the security considerations that affect non-open source software. In fact, the decentralized nature of the open source development model poses some unique security challenges, such as widespread use of outdated versions and exposure to known security vulnerabilities that go undetected and unpatched.
So, how best to leverage the benefits from open source building blocks while protecting your organization from some of the risks and vulnerabilities? And how to do that in a way that does not slow down your development velocity? Let's explore.
A Simple Build For Container Environments
First, embrace the use of a container as the runtime environment for your application. Take a minimalist approach to the construction of the container, so that only the open source packages which your application requires are included. This will limit the number of potential vulnerabilities that the container may be exposed to. You will want to ensure that these open source packages are kept up to date over time.
Container Image Scanning Automation
Secondly, incorporate an automated container scanning tool that is integrated into your software development process. This is where Anchore Enterprise can help.
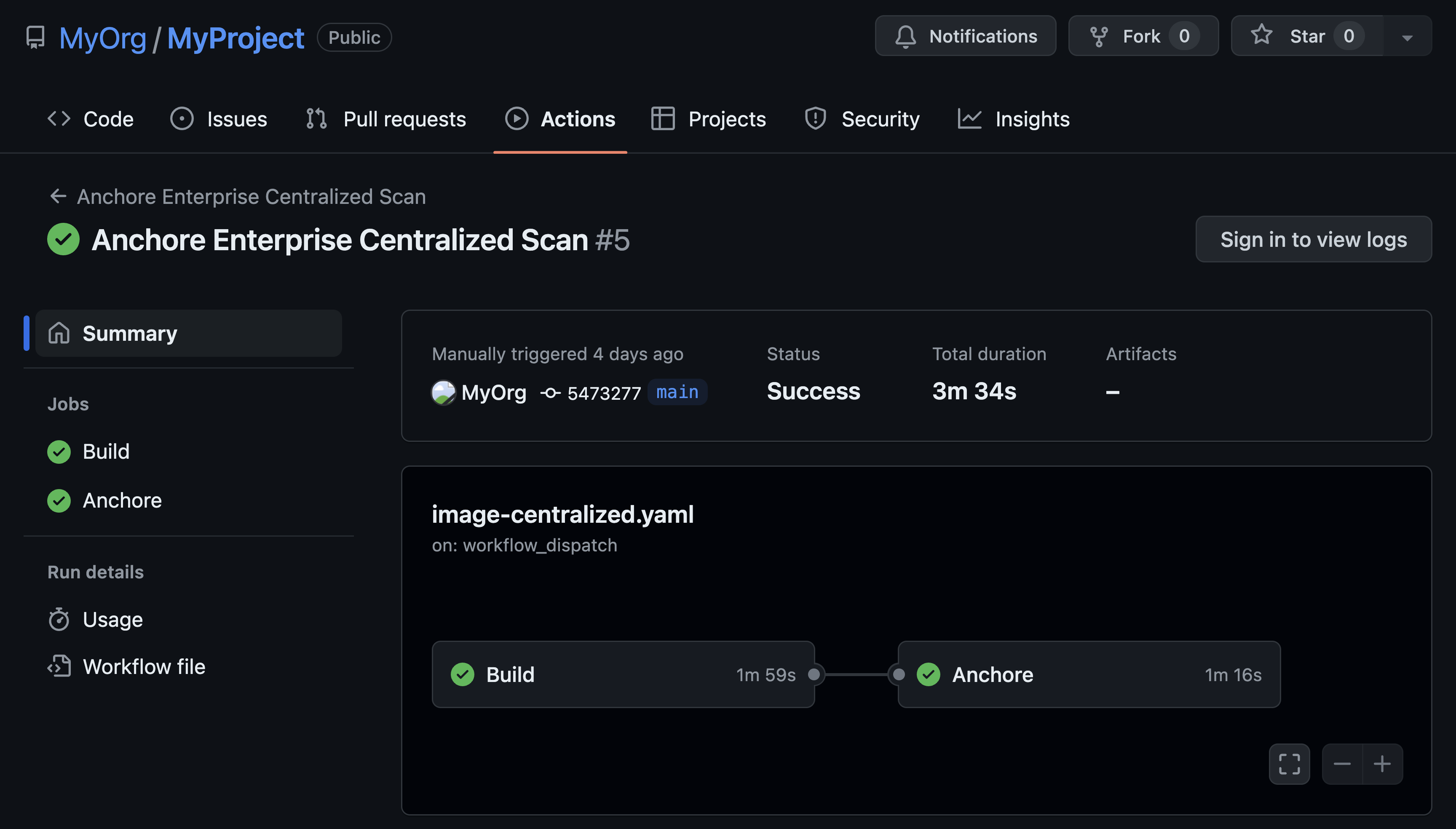
Anchore Enterprise plugs into your CI/CD pipeline so that each container is scanned according to a set of policies that you control, and this scanning is done in a way that is not only automated, it is done before the application’s container is deployed into a production environment. Incorporating the hardening process into the development cycle is the defining element of what we mean by DevSecOps.
Anchore Enterprise conducts a deep inspection of the container and scans package versions against several vulnerability databases such as VulnDB and NVD. This mechanism ensures that your application’s container will not be exposed to any known security vulnerabilities at the time when it goes into production.
Security Measures For Outdated Open Source
But what about outdated versions of open source packages? Anchore Enterprise allows additional controls to be set so that the policies can be fine-tuned to your organization’s requirements. For example, certain packages or package versions can be explicitly prohibited from inclusion into the production environment via use of the policy blacklist. In this manner, you could ensure that outdated versions of open source packages could trigger a stop-build event, not because there are any known vulnerabilities but simply because those package versions are outdated and unmaintained.
Perhaps most importantly, these security-enhancing mechanisms are performed in a highly automated manner, so that each of the open source components in your development stack are scanned and validated according to the policy automatically every time your application is built.
As a result, your software development teams can take advantage of the compelling advantages that these technologies have to offer, while also providing an automated, low-friction way of guarding against the risks inherent with the decentralized open source development model.