Jan 26th @ 2pm EST/11am PST
Author: teamanchore
FedRAMP Pre-Assessment Playbook for Containers
2022 Security Trends: Software Supply Chain Survey
In January 2022, Anchore published its Software Supply Chain Security Survey of the latest security trends, with a focus on the platforms, tools, and processes used by large enterprises to secure their software supply chains, including the growing volume of software containers.
What Are the 2022 Top Security Trends?
The top 2022 security trends related to software supply chain security are:
- Supply chain attacks are impacting 62 percent of organizations
- Securing the software supply chain is a top priority
- The software bill of materials (SBOM) emerges as a best practice to secure the software supply chain
- Open source and internally developed code both pose security challenges
- Increased container adoption is driving the need for better container security
- Scanning containers for vulnerabilities and quickly remediating them is a top challenge
- The need to secure containers across diverse environments is growing as organizations adopt multiple CI/CD tools and container platforms
Software Supply Chain Security Survey: Key Findings
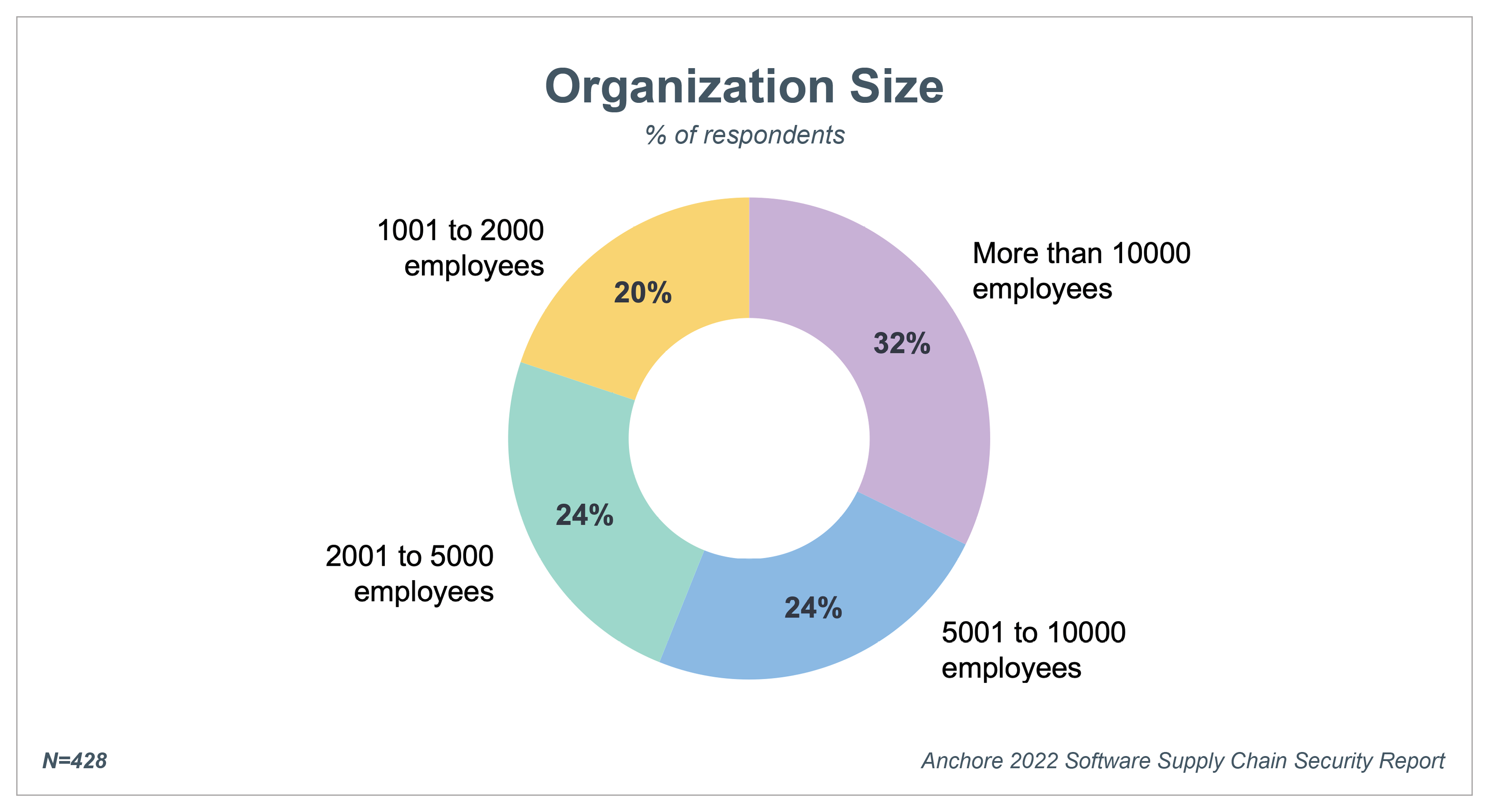
The Anchore Software Supply Chain Security Survey is the first survey of respondents exclusively from large enterprises rather than solely from open source and developer communities or smaller organizations. The survey asked 428 executives, directors, and managers in IT, security, development, and DevOps functions about their security practices and concerns and use of technologies for securing containerized applications. Their answers provide a comprehensive perspective on the state of software supply chain security with a focus on the impact of increased use of software containers.
We highlight several key findings from the survey in this blog post. For the complete survey results, download the Anchore 2022 Software Supply Chain Security Report.
1. Supply chain attacks impacted 62% of organizations
Such widespread attacks as SolarWinds, MIMECAST, and HAFNIUM as well as the recent Log4j vulnerability have brought the realities of the risk associated with software supply chains to the forefront. As a result, organizations are quickly mobilizing to understand and reduce software supply chain security risk.
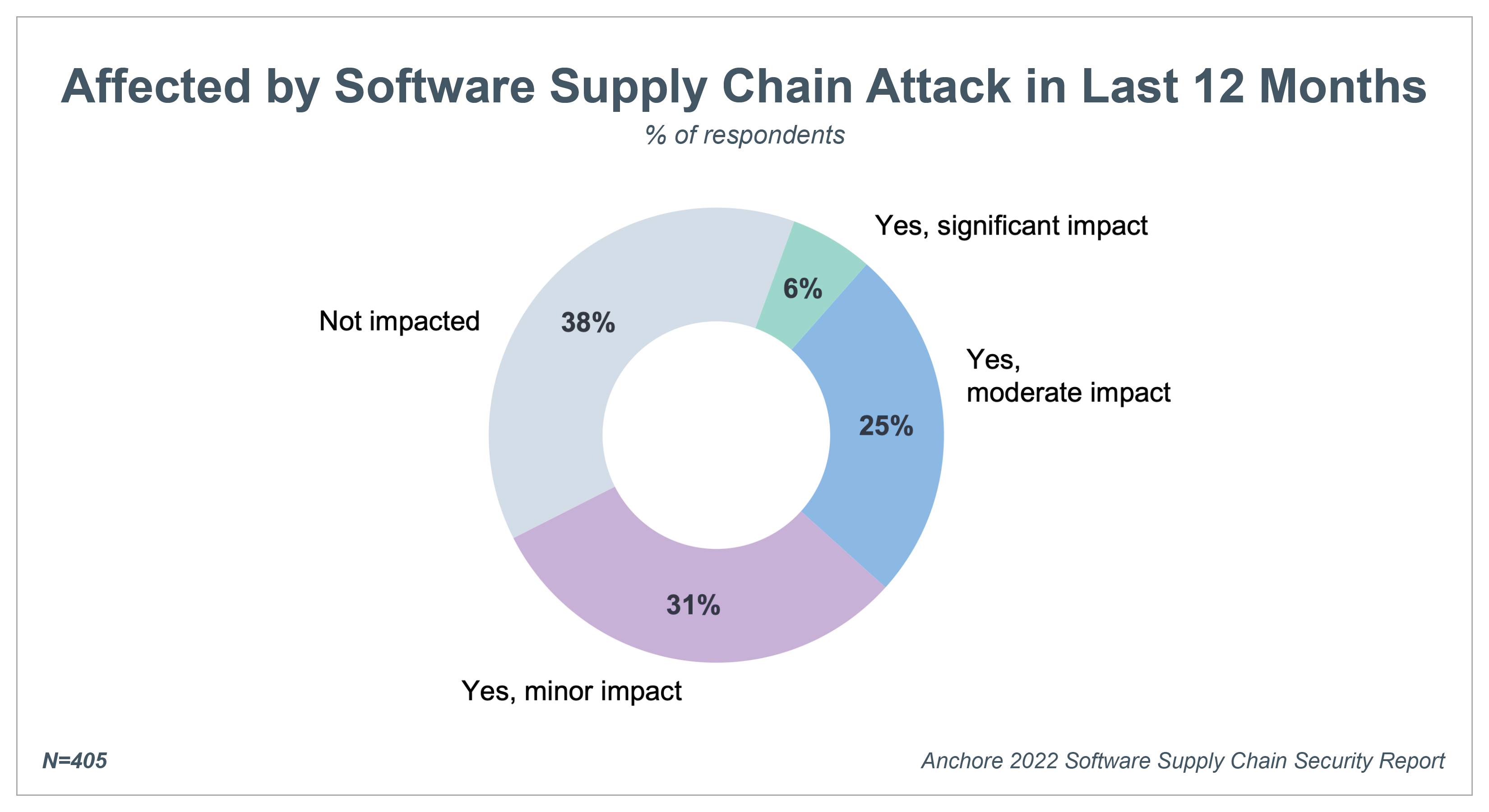
A combined 62 percent of respondents were impacted by at least one software supply chain attack during 2021, with 6 percent reporting the attacks as having a significant impact and 25 percent indicating a moderate impact.
2. Organizations focus on securing the software supply chain
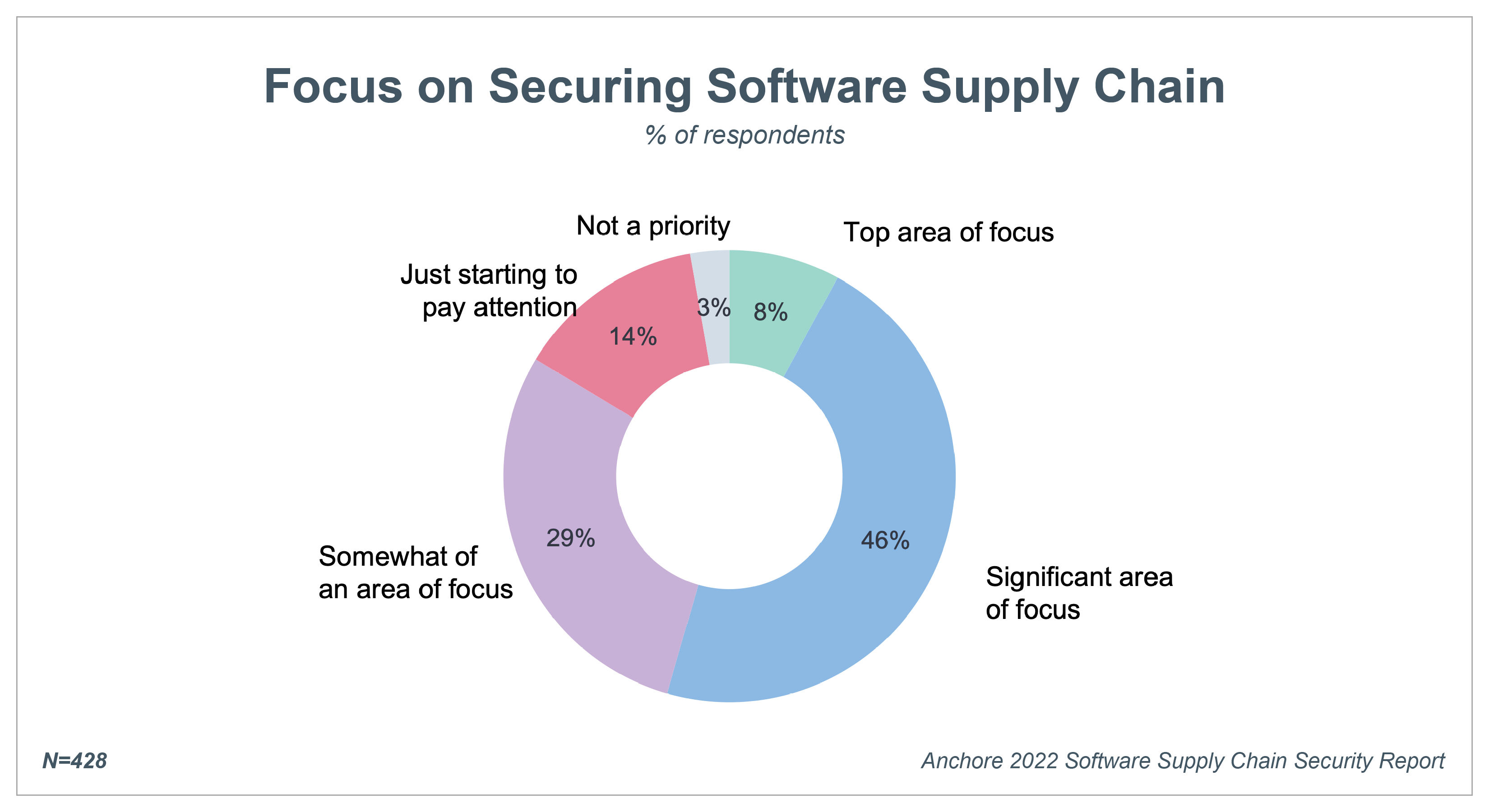
More than half of survey respondents (54 percent) indicate that securing the software supply chain is a top or significant focus, while an additional 29 percent report that it is somewhat of a focus. This indicates that recent, high-profile attacks have put software supply chain security on the radar for the vast majority of organizations. Very few (3 percent) indicate that it is not a priority at all.
3. SBOM practices must mature to improve supply chain security
The software bill-of-materials (SBOM) is a key part of President Biden’s executive order on improving national cybersecurity because it is the foundation for many security and compliance regulations and best practices. Despite the foundational role of SBOMs in providing visibility into the software supply chain, fewer than a third of organizations are following SBOM best practices. In fact, only 18 percent of respondents have a complete SBOM for all applications.
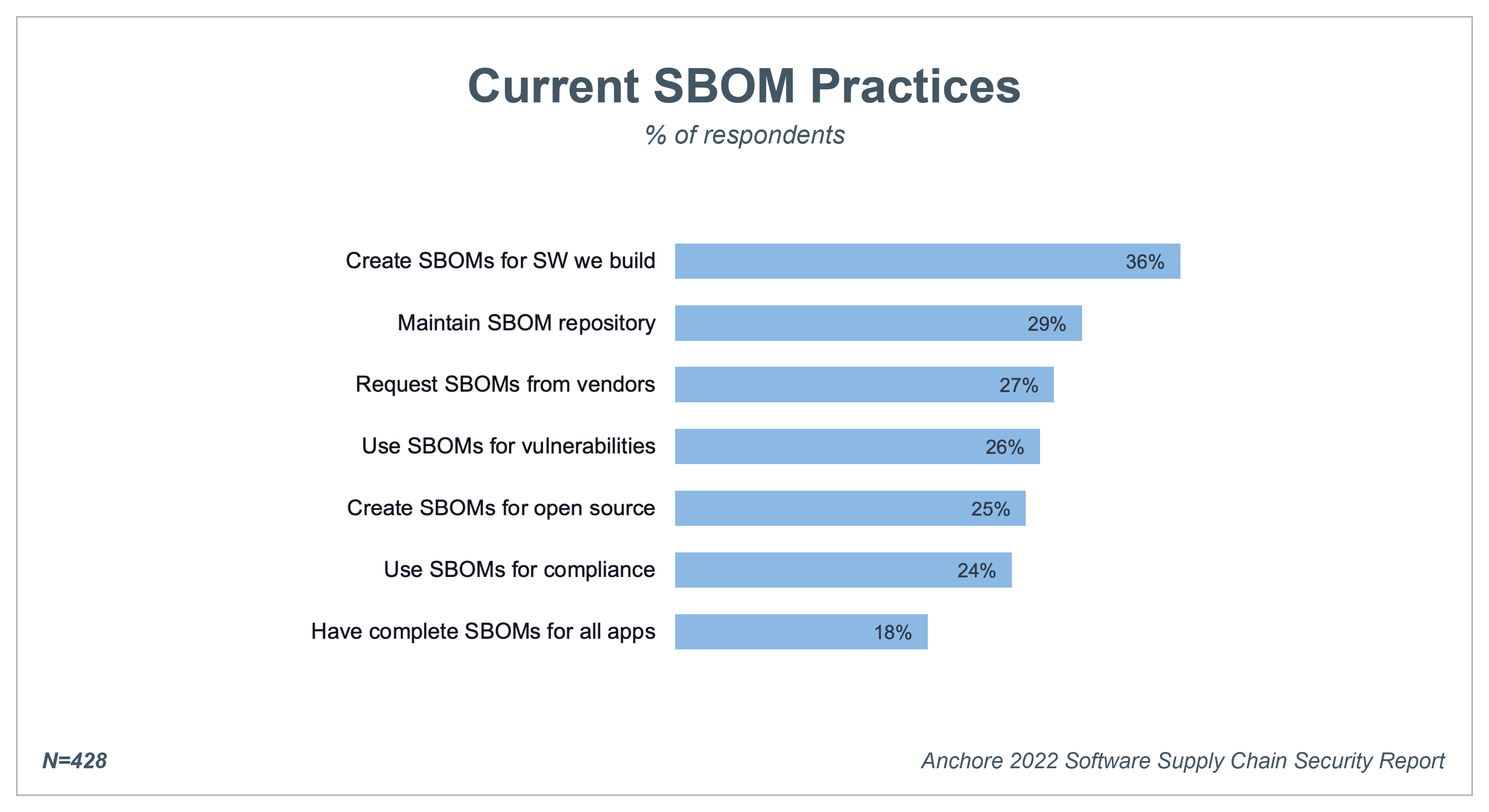
Despite these low numbers, respondents do report, however, that they plan to increase their SBOM usage in 2022, so these trends may change as adoption continues to grow.
4. The shift to containers continues unabated
Enterprises plan to continue expanding container adoption over the next 24 months with 88 percent planning to increase container use and 31 percent planning to increase use significantly.
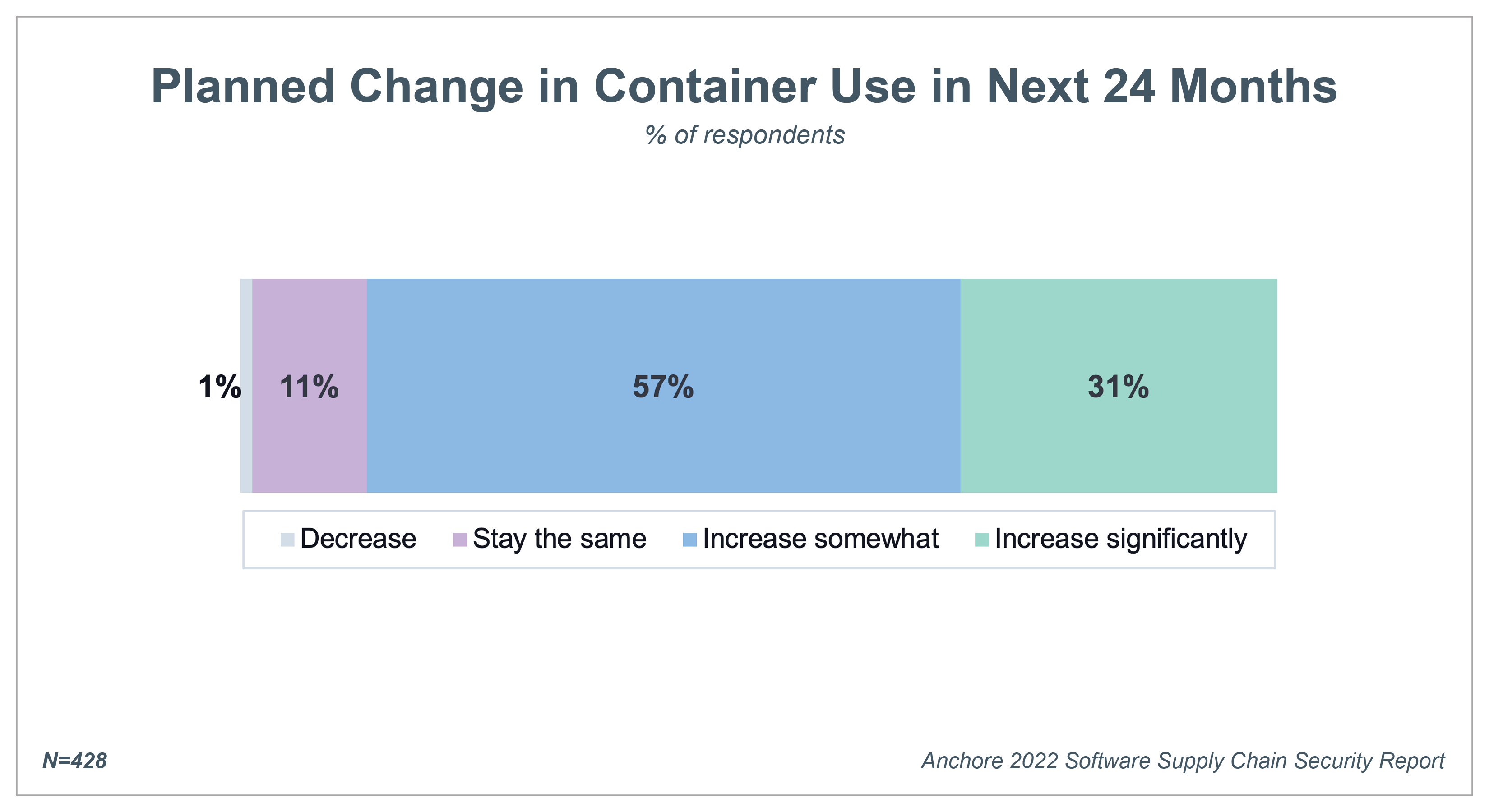
A related trend of note is that more than half of organizations are now running employee- and customer-facing applications in containers.
5. Securing containers focuses on supply chain and open source
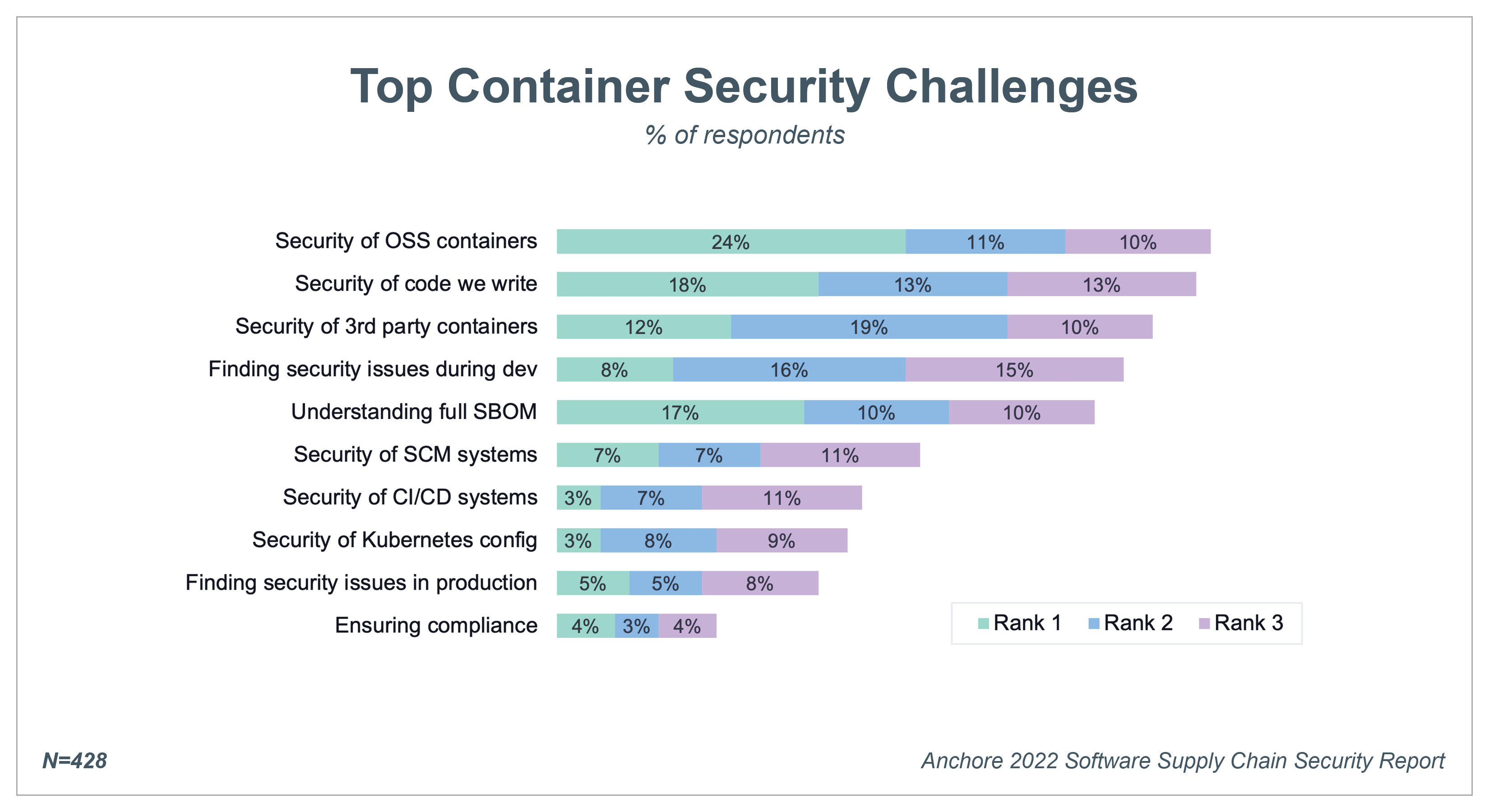
Developers incorporate a significant amount of open source software (OSS) in the containerized applications they build. As a result, the Security of OSS containers is ranked as the number one challenge by 24 percent of respondents with almost half (45 percent) ranking it among their top three challenges. Ranked next was Security of the code we write with 18 percent of respondents choosing that as their top container security challenge and Understanding full SBOM with 17 percent.
6. Organizations face challenges in scanning containers
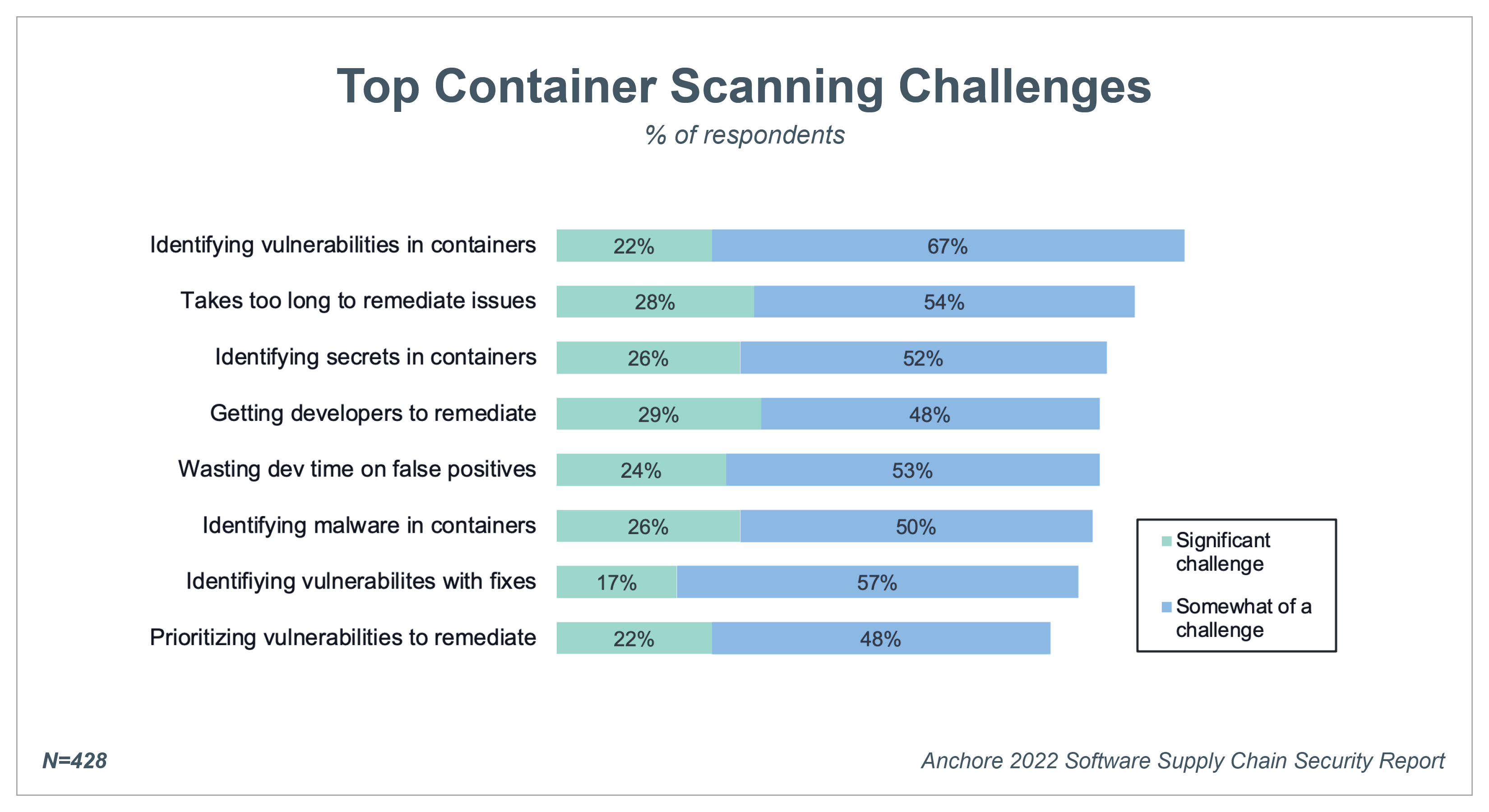
As organizations continue to expand their container use, a large majority face critical challenges related to identifying and remediating security issues within containers. Top challenges include identifying vulnerabilities in containers (89 percent), the time it takes to remediate issues (72 percent), and identifying secrets in containers (78 percent). Organizations will need to adopt more accurate container scanning tools that can accurately pinpoint vulnerabilities and provide recommendations for quick remediation.
7. Organizations must secure across diverse environments
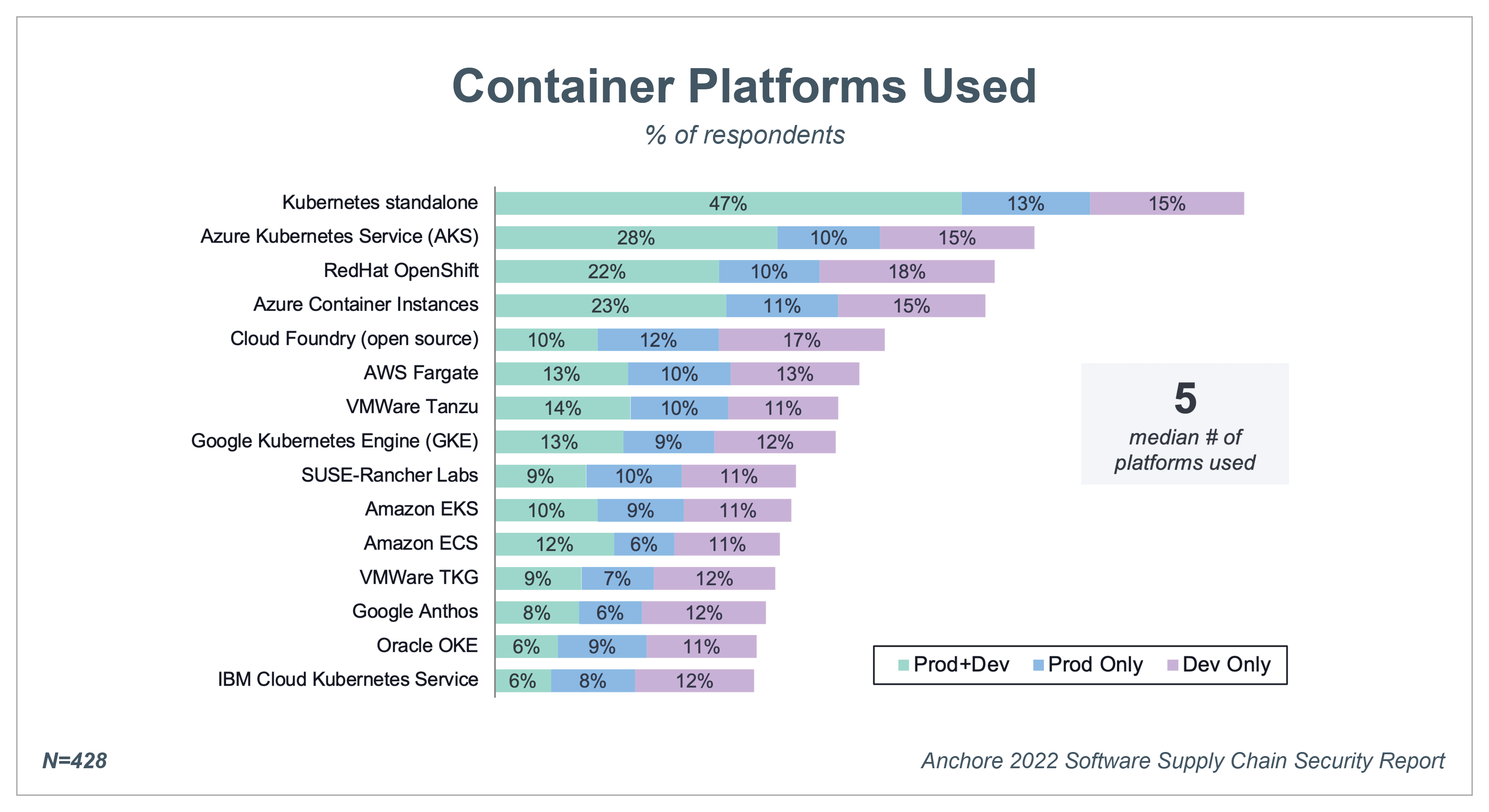
Survey respondents use a median of 5 container platforms.The most popular method of deployment is standalone Kubernetes clusters based on the open source package, which 75 percent of respondents use. These environments are run on-premises, via hosting providers, or on infrastructure-as-a-service from a cloud provider. The second most popular container platform is Azure Kubernetes Service (AKS) with 53 percent of respondents using, and Red Hat OpenShift ranks third at 50 percent. Respondents leverage the top container platforms in both their production and development environments.
For more insights to help you build and maintain a secure software supply chain, download the full Anchore 2022 Software Supply Chain Security Report.
Attribution Requirements for Sharing Charts
Anchore encourages the reuse of charts, data, and text published in this report under the terms of the Creative Commons Attribution 4.0 International License.
You may copy and redistribute the report content according to the terms of the license, but you must provide attribution to the Anchore 2022 Software Supply Chain Security Report.
2022 Software Supply Chain Security Report
7 Software Supply Chain Security Actions to Take in 2022
Join us Jan 12th @ 2pm EST/11am PST to learn how to plan your “Day 2” for Log4j and future zero-day vulnerabilities, leverage SBOMs as a foundation for supply chain security, and expand automation against malware, cryptomining, and leaked secrets.
InfoWorld: How to detect the Log4j vulnerability in your applications
A bug in the ubiquitous Log4j library can allow an attacker to execute arbitrary code on any system that uses Log4j to write logs. Does yours?
InfoWorld: Why SBOM management is no longer optional
Security Boulevard: The Dangers of a Log4j Worm
Key Things to Know about SBOMs and SBOM Standards
This blog post has been archived and replaced with the support pillar page here: https://anchore.com/wp-admin/post.php?post=987473316&action=edit
The blog post is meant to remain “public” so that it will continue to show on the /blog feed. This will help discoverability for people browsing the blog and potentially help SEO. If it is clicked on it will automatically redirect to the pillar page.
Find the Log4j Vulnerability with Anchore Enterprise
This tutorial video shows how to identify and triage the Log4j vulnerability using Anchore Enterprise. It details how to validate in runtime, the CISA policy bundle, automated policy function, automated enforcement function, and visibility to see if Log4j was inherited from a base image.