Source code is the cornerstone of software development and if not stored and managed securely, could lead to the collapse of your entire pipeline. In this webinar we’ll look at the top four best practices for securing your source code repositories.
Author: teamanchore
Gartner Innovation Insight for SBOMs
The software bill or materials, or SBOM, is foundational for end-to-end software supply chain management and security. Knowing what’s in software is the first step to securing it. Think of an SBOM like an ingredients label on packaged food: If there’s a toxic chemical in your can of soup, you’d want to know before eating it.
SBOMs are critical not only for identifying security vulnerabilities and risks in software but also for understanding how that software changes over time and potentially becomes vulnerable to new threats. In Innovation Insight for SBOMs, Gartner recommends integrating SBOMs throughout the software development lifecycle to improve the visibility, transparency, security, and integrity of proprietary and open-source code in software supply chains.
The Role of SBOMs in Securing Software Supply Chains
Gartner estimates that by 2025, 60 percent of organizations building or procuring critical infrastructure software will mandate and standardize SBOMs in their software engineering practice — a significant increase from less than 20 percent in 2022. However, organizations that are using open-source software and reusable components to simplify and accelerate software development are challenged with gaining visibility into the software they consume, build, and operate. And without visibility, they become vulnerable to the security and licensing compliance risks associated with software components.
SBOMs are an essential tool in your security and compliance toolbox. They help continuously verify software integrity and alert stakeholders to security vulnerabilities and policy violations.
To achieve software supply chain security at scale, Gartner recommends that software engineering leaders integrate SBOMs into their DevSecOps pipelines to:
- Automatically generate SBOMs for all software produced
- Automatically verify SBOMs for all open source and proprietary software consumed
- Continuously assess security and compliance risks using SBOM data before and after deployment
Gartner underscores the importance of integrating SBOM workflows across the software development lifecycle, noting that “SBOMs are an essential tool in your security and compliance toolbox. They help continuously verify software integrity and alert stakeholders to security vulnerabilities and policy violations.”
Who Should Use SBOMs
Citing U.S. National Telecommunications and Information Administration (NTIA) recommendations, Gartner identifies three primary entities that benefit from SBOM adoption:
- Software producers: Use SBOMs to assist in the building and maintenance of their supplied software
- Software procurers: Use SBOMs to inform pre-purchase assurance, negotiate discounts, and plan implementation strategies
- Software operators: Use SBOMs to inform vulnerability management and asset management, to manage licensing and compliance, and to quickly identify software and component dependencies and supply chain risks
SBOM Tools Evaluation
Gartner cautions that SBOMs are not intended to be static documents and that every new release of a component should include a new SBOM. When evaluating open-source and commercial SBOM tools for SBOM generation and management, Gartner advises organizations to select tools that provide the following capabilities:
- Create SBOMs during the build process
- Analyze source code and binaries (like container images)
- Generate SBOMs for those artifacts
- Edit SBOMs
- View, compare, import, and validate SBOMs in a human-readable format
- Merge and translate SBOM contents from one format or file type to another
- Support use of SBOM manipulation in other tools via APIs and libraries
By generating SBOMs in the build phase, developers and security teams can identify and manage the software in their supply chains and catch bad actors early before they reach runtime and wreak havoc.
New Gartner Report: Innovation Insight for SBOMs
How to Meet the 6 FedRAMP Vulnerability Scanning Requirements for Containers
If you are tasked with implementing FedRAMP security controls for containerized workloads, this webinar is for you. We’ll walk you through a step-by-step process to explain how Anchore Enterprise can help you prepare a response for each of the six scanning requirements outlined in the FedRAMP Vulnerability Scanning Requirements for Containers.
SBOM-powered Software Supply Chain Management
SBOMs are quickly becoming the foundational element of software supply chain security. With the release of Anchore Enterprise 4.0, we are building on our existing SBOM capabilities to create the first SBOM-powered software supply chain management solution.
Anchore Enterprise 4.0 Delivers SBOM-Powered Software Supply Chain Management
With significant attacks against the software supply chain over the last year, securing the software supply chain is top of mind for organizations of all sizes. Anchore Enterprise 4.0 is designed specifically to meet this growing need, delivering the first SBOM-powered software supply chain management tool.
Powered By SBOMs
Anchore Enterprise 4.0 builds on Anchore’s existing SBOM capabilities, placing comprehensive SBOMs as the foundational element to protect against threats that can arise at every step in the software development lifecycle. Anchore can now spot risks in source code dependencies and watch for suspicious SBOM drift in each software build, as well as monitor applications for new vulnerabilities that arise post-deployment.
New Key Features:
Track SBOM drift to detect suspicious activity, new malware, or compromised software
Anchore Enterprise 4.0 introduces an innovative new capability to detect SBOM drift in the build process, alerting users to changes in SBOMs so they can be assessed for new risks or malicious activity. With SBOM drift detection, security teams can now set policy rules that alert them when components are added, changed, or removed so that they can quickly identify new vulnerabilities, developer errors, or malicious efforts to infiltrate builds.
End-to-end SBOM management reduces risk and increases transparency in software supply chains
Building on Anchore’s existing SBOM-centric design, Anchore Enterprise 4.0 now leverages SBOMs as the foundational element for end-to-end software supply chain management and security. Anchore automatically generates and analyzes comprehensive SBOMs at each step of the development lifecycle. SBOMS are stored in a repository to provide visibility into your components and dependencies as well as continuous monitoring for new vulnerabilities and risks, even post-deployment. Additionally, users can now meet customer or federal compliance requirements such as those described in the Executive Order On Improving the Nation’s Cybersecurity by producing application-level SBOMs to be shared with downstream users.
Track the security profile of open source dependencies in source code repositories and throughout the development process
With the ever-expanding use of open source software by developers, it has become imperative to identify and track the many dependencies that come with each piece of open source at every step of the development cycle to ensure the security of your software supply chain. Anchore Enterprise 4.0 extends scanning for dependencies to include source code repositories on top of existing support for CI/CD systems and container registries. Anchore Enterprise can now generate comprehensive SBOMs that include both direct and transitive dependencies from source code repositories to pinpoint relevant open source vulnerabilities, and enforce policy rules.
Gain an application-level view of software supply chain risk
Securing the software supply chain requires visibility into risk for each and every application. With Anchore Enterprise 4.0, users can tag and group all of the artifacts associated with a particular application, release, or service. This enables users to report on vulnerabilities and risks at an application level and monitor each application release for new vulnerabilities that arise. In the case of a new vulnerability or zero-day, users can quickly identify impacted applications solely from the SBOM repository and respond quickly to protect and remediate those applications.
Looking Forward
Anchore believes that SBOMs are the foundation of software supply chain management and security. The Anchore team will continue to build on these capabilities and advance the use of SBOMs to secure and manage the ever-evolving software supply chain landscape.
Policy-Based Compliance for Containers: CIS, NIST, and More
Policies are an integral part of ensuring security and compliance, but what does “policy-based compliance” mean in the world of cloud-native software development? How can policies be automated to ensure the security of your container images?
Helping Entrepreneurs Take Flight
The Kindness Campaign, inspired by Anchore’s core values, focuses on spreading kindness throughout our local communities. With Anchorenauts distributed across the US and UK, our quarterly volunteer program enables and encourages Anchorenauts to connect with local organizations and give back. In addition to direct support for various causes throughout the year, Anchore empowers team members to get involved with eight (8) paid volunteer hours per quarter.
This month, we are excited to partner with Ashley Goldstein from the Santa Barbara based organization, Women’s Economic Ventures (WEV). WEV, in partnership with Mixteco Indigena Community Organization Project (‘MICOP”), programatically supports aspiring entrepreneurs within the Indigenous and Latinx community in Santa Barbara and Ventura Counties.
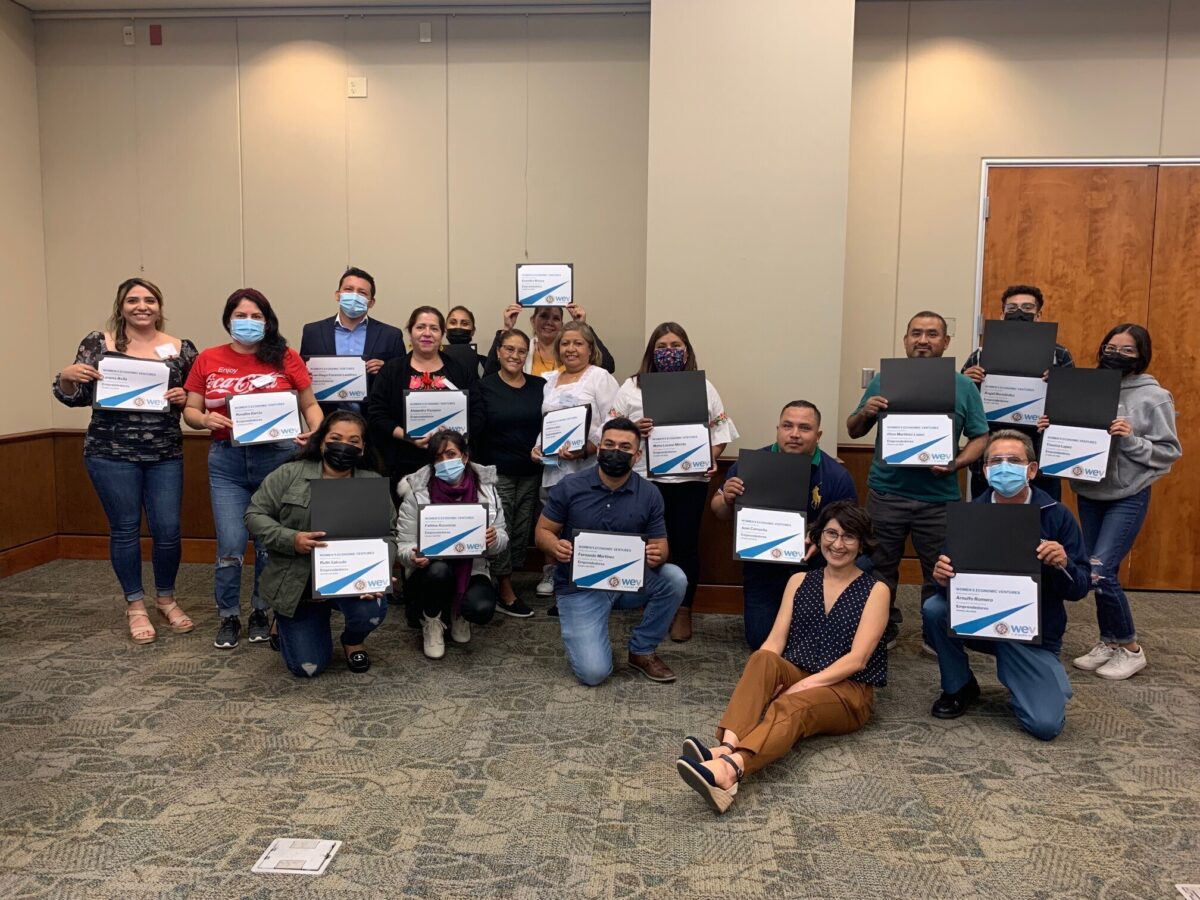
Through the Los Emprendedores Program, Ashley firmly believes in the WEV’s and MICOP’s ability to empower members with the skills they need to launch their own businesses and to effect change in the most marginalized populations.
As part of the Kindness Campaign, Anchore has donated gently used Apple MacBooks to support budding entrepreneurs with the tools needed to kick start their businesses and enable their tremendous entrepreneurship training in the Los Emprendedores Program. In the program, participants develop highly valuable business skills ranging from business planning, grant writing, digital marketing, and key ESG (Environmental, Social, & Governance) practices.
As a tech company, we deeply believe in the responsibility to give back a piece of the industry to our community through widening access to both basic technology, but also business and career opportunities in the technology sector. At Anchore, we feel a great sense of pride in playing a part in contributing to that in our community, and are grateful for the opportunity to support Ashley, WEV, and MICOP.
How You Can Take Action
If your company has gently used computer equipment that is ready to be donated, we encourage you to reach out to WEV, and other organizations doing amazing work in their communities such as Boys & Girls Clubs of America (that have local chapters nationwide) to learn more about the ways you can help.
Be sure to check back next quarter to hear about new activity with Anchore’s Kindness Campaign.
Best Practices for Securing Open Source Software for Enterprises
Open source software is everywhere, and it’s here to stay. Yet 45% of respondents to Anchore’s 2022 Software Supply Chain Security Report still cite securing OSS as their top container security challenge.
2022 Trends in Software Supply Chain Security
Anchore surveyed hundreds of security and DevOps leaders at large enterprises on their software supply chain security practices. Their answers reveal that a top trend in 2022 is a focus on securing software supply chains as the use of software containers continues to rise.