Manual security checks are the enemy of speed. For Federal System Administrators and ISSOs, “stigging” a system manually (going line-by-line through hundreds of XML checks) is not only tedious; it’s impossible at the scale of modern software factories.
With the Department of Defense (DoD) moving toward continuous Authority to Operate (cATO), the days of manually creating .ckl files once every 90 days are over. To meet the requirements of the Risk Management Framework (RMF) without halting deployment, automation is the only path forward.
In this post, we break down the top tools for 2025, categorized by their specific role in your infrastructure; from traditional OS hardening to modern container security.
At a Glance: Top STIG Compliance Tools
If you are looking for the right tool for a specific job, here is the quick breakdown:
| Tool | Best For | Type | Cost |
|---|---|---|---|
| Anchore Enterprise | Containers & Kubernetes | Automated Compliance Platform | Commercial |
| DISA STIG Viewer | Viewing Manual Checklists | Desktop Utility | Free (Gov) |
| SCAP Compliance Checker (SCC) | Local OS Scanning | Scanner | Free (Gov) |
| MITRE SAF | DIY DevSecOps / Custom Profiles | Open Source Framework | Free (Open Source) |
| SteelCloud ConfigOS | Windows/Linux Remediation | Remediation Tool | Commercial |
| Tenable.sc (ACAS) | Network & VM Scanning | Vulnerability Management | Commercial |
| Evaluate-STIG | Documentation/Checklists | Documentation Utility | Free (Gov) |
Essential Free Utilities
Every federal engineer needs these two utilities installed. They are the “gold standard” provided directly by DISA and are often the baseline against which other tools are measured.
1. DISA STIG Viewer
Type: Desktop Utility (Java)
Best For: Manually viewing STIGs and creating .ckl files.
The DISA STIG Viewer is the official tool for viewing XCCDF (eXtensible Configuration Checklist Description Format) files. It allows you to import a STIG, view the specific requirements (Vuln IDs, Rule IDs), and manually mark them as Open, Closed, or Not Applicable.
- Pros: It is the official system of record. If you are submitting a checklist to an ISSO, it usually needs to be in a format this tool can read.
- Cons: It is entirely manual. It does not “scan” your system; it is simply a digital clipboard for you to record your findings.
2. SCAP Compliance Checker (SCC)
Type: Local Scanner
Best For: Ad-hoc scanning of local Windows or Linux servers.
SCC is DISA’s comprehensive scanning tool. Unlike the STIG Viewer, SCC actually scans the target operating system against the SCAP (Security Content Automation Protocol) content. It produces a compliance score and a detailed report of which settings failed.
- Pros: Extremely accurate for traditional Operating Systems (RHEL, Windows Server).
- Cons: It is a “point-in-time” scanner. It doesn’t scale well for cloud-native environments or CI/CD pipelines where containers are created and destroyed in minutes.
Best Tools for Container & Cloud-Native STIG Compliance
Traditional tools often struggle with containers. They treat a container like a small server, attempting to SSH in and scan it—a practice that breaks the immutable nature of containers. For modern DoD Software Factories, you need tools built for the cloud-native stack.
3. Anchore Enterprise
Type: Container Security & Compliance Platform
Best For: DoD Software Factories, Kubernetes, and CI/CD Pipelines.
Anchore Enterprise is built to solve the specific challenge of securing the software supply chain. Unlike traditional scanners that wait until a system is running to check it, Anchore scans container images before they are deployed.
Why it stands out:
Legacy scanners (like ACAS) often can’t see inside the layers of a container image effectively, leading to false positives or missed findings. Anchore analyzes the image contents—packages, binaries, and configuration files—and matches them against DoD-specific policy packs.
- Automated Gates: Block builds in Jenkins/GitLab if they fail STIG checks (e.g., a container running as root).
- Policy-as-Code: Define your STIG policies once and enforce them across every build, ensuring that only compliant images ever reach your Kubernetes cluster.
- Remediation: Provides clear guidance to developers on why a build failed, reducing the friction between security and engineering.
View Anchore’s Public Sector Solutions
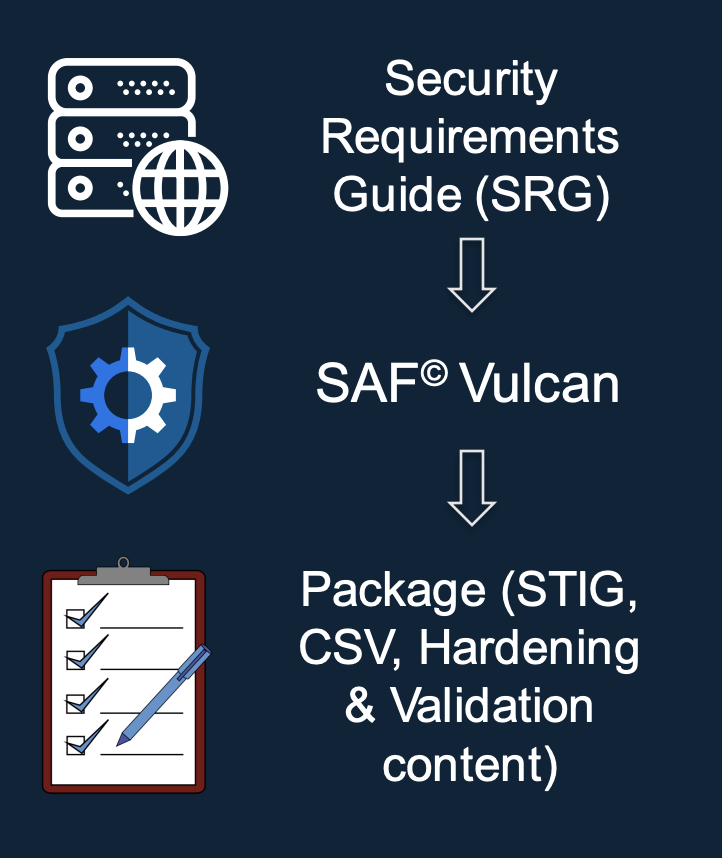
4. MITRE SAF (Security Automation Framework)
Type: Open Source Framework
Best For: DIY DevSecOps teams building custom validation profiles.
MITRE SAF is an open-source project that brings together testing libraries (like InSpec) and data converters to visualize security data. It is excellent for teams that want to write custom tests (“InSpec profiles”) to validate specific application configurations that standard STIGs might miss.
- Connection: Anchore collaborates with the MITRE SAF team to ensure that compliance data can be shared and visualized effectively across different platforms.
Best Tools for Traditional OS & Network Hardening
For the “iron” of your data center—routers, switches, and bare-metal servers—these tools remain the industry heavyweights.
5. SteelCloud ConfigOS
Type: Remediation Automation
Best For: Mass-remediation of Windows/Linux servers.
While most tools find the problem, SteelCloud’s ConfigOS is famous for fixing it. It automates the remediation process, effectively “healing” the system to bring it into compliance with the STIG.
- Key Feature: Its “Remediation with Rollback” capability allows admins to apply STIG controls to thousands of endpoints and roll them back if a configuration breaks a critical application.
6. Tenable.sc / ACAS
Type: Vulnerability Management
Best For: General network scanning and continuous monitoring.
In the DoD, you will know this simply as ACAS (Assured Compliance Assessment Solution). It is the mandated vulnerability scanning suite for government networks.
- Context: ACAS is powerful for mapping your network and finding unpatched servers. However, for DevSecOps teams, reliance solely on ACAS can be a bottleneck, as scans often happen late in the staging environment rather than in the build pipeline.
7. SolarWinds Network Configuration Manager (NCM)
Type: Network Management
Best For: Network engineers managing Cisco/Juniper switches.
For the network layer, SolarWinds NCM provides automated config backups and vulnerability assessments. It can automatically check device configurations against NIST and DISA STIG standards to ensure a router hasn’t drifted out of compliance.
Best Tools for Documentation & Checklist Automation
8. Evaluate-STIG (NAVSEA)
Type: Documentation Utility
Best For: Automating the creation of .ckl files.
Originally developed by NAVSEA, Evaluate-STIG is a utility designed to bridge the gap between raw scan data and the manual checklist. It allows you to import scan results (from SCC or ACAS) and automatically populate the corresponding checks in the STIG checklist.
- Why it matters: It drastically reduces the “paperwork fatigue” of compliance, allowing ISSOs to focus on the open findings rather than manually checking boxes for passing items.
Implementation Tips for STIG Automation
Adopting tools is only half the battle. Here is how to implement them effectively in a DevSecOps workflow:
- Map specific CCIs to your controls:
Don’t just “scan for STIGs” in a vacuum. You need to know which Control Correlation Identifiers (CCIs) map to your required NIST 800-53 controls. This mapping is what allows you to prove to an assessor that your automated scan actually satisfies a specific security requirement. - Shift Left (for real):
Waiting for a scan in the staging environment is too late. By the time a vulnerability is caught there, the developer has already moved on to the next task. Use tools like Anchore to fail builds in the CI/CD pipeline immediately if they violate STIG policies. This creates a tight feedback loop and cheaper remediation. - Automate the “Not Applicable” findings:
A huge part of STIG fatigue is reviewing items that simply don’t apply to your architecture. Use overlays or policy files to permanently mark irrelevant checks as “N/A” (with justification). This ensures your engineers stop reviewing the same irrelevant findings every week.
Choosing the Right Tool for the Mission
There is no single “magic bullet” for compliance. A robust RMF strategy requires a stack of tools:
- SCC & STIG Viewer for your baseline, ad-hoc checks.
- ACAS (Tenable) for your network-wide vulnerability management.
- Anchore Enterprise to secure the containers and software supply chain that run your modern applications.
Modern DoD software factories cannot rely on manual checklists. Automation is not just about saving time; it is the only way to move at the speed of the mission while maintaining a hard security posture.