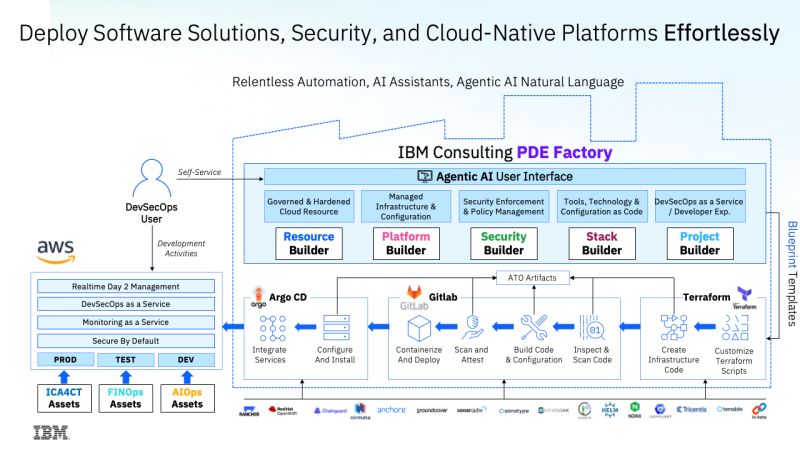
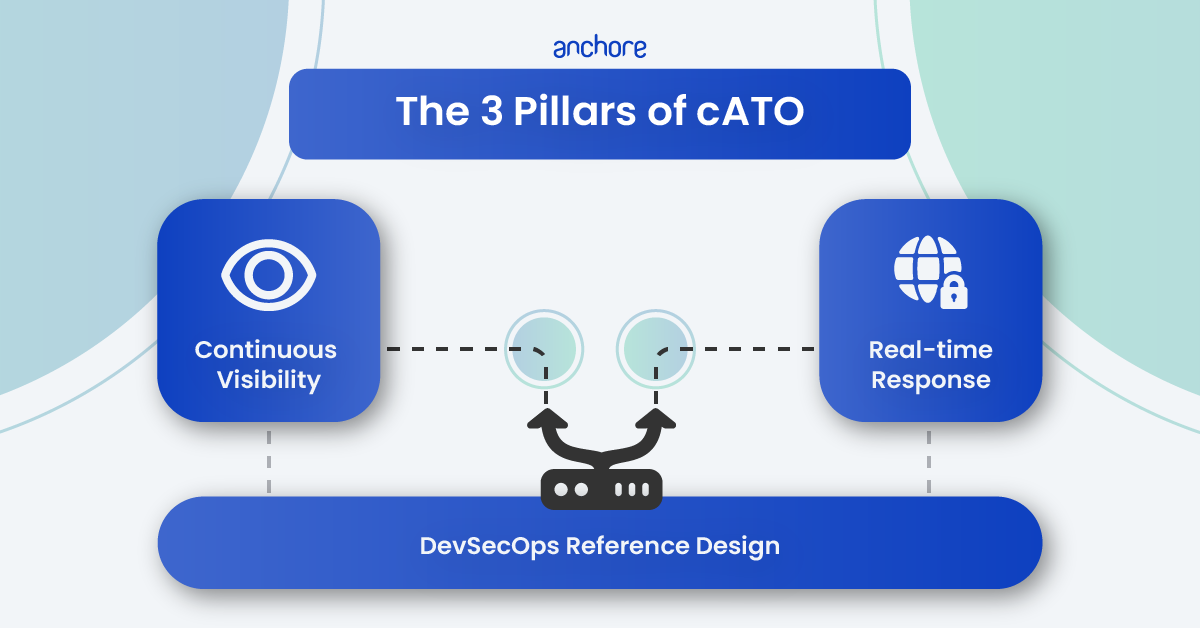
The DoD, Contractors, and Federal Systems Integrators (FSIs) are increasingly leveraging DevSecOps to iterate and deploy software. As a result, the DoD DevSecOps Reference Design is the canonical architecture for the entire defense industrial base (DIB). In many cases, it is even contractually required.
The goal of this Reference Design is to automate, monitor, and apply security at all phases of the software development lifecycle. It organizes software development into a (DoD) software factory, which is broken down into distinct phases. Each phase contains specific activities and tools designed to automate security and quality checks. Anchore Enterprise is tightly integrated with these phases, tools, and activities.
Software Factory Tools and Activities – Section 4.2
The DoD software factory relies on integrating security directly into your developer workflows. Anchore Enterprise supports this by acting as a seamless guardrail during the earliest stages of the software lifecycle.
The Develop Phase
A critical requirement during the Develop phase is evaluating source code for vulnerable packages. Anchore Enterprise handles this by generating an SBOM (Software Bill of Materials). This allows it to deeply scan source code repositories for known vulnerabilities. Using policy-as-code, Anchore can automatically stop CI/CD pipeline build promotions. If vulnerable or non-compliant content is found, risky code never advances to the next stage.
The Build Phase
Managing dependencies and artifact repositories is essential during the Build phase. Anchore generates a comprehensive SBOM from container images, filesystems, VMDKs, and open source code. This helps teams understand and store build dependencies as deliverable artifacts. Additionally, Anchore continuously monitors and scans containers within your artifact repositories. This actively detects vulnerabilities, policy violations, exposed secrets, and malware.
The Test Phase
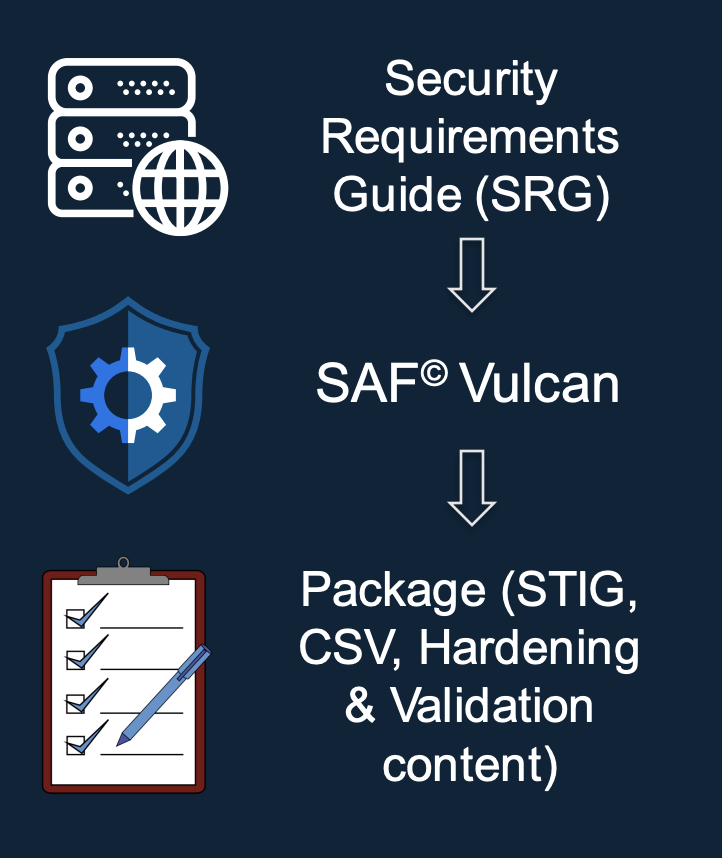
The Test phase focuses on hardening and ensuring compliance. Anchore provides robust software license compliance checking. It uses policy gates to enforce acceptable use for open source distributions. Anchore also acts as a primary container security tool. It hardens containers to meet Authorizing Official (AO) and regulatory requirements via policy-as-code. You can leverage POA&M-as-code through allowlisting to set time-based dates for authorized exceptions. Furthermore, Anchore scans containers against DISA STIGs and frameworks like NIST 800-53 or 800-190. It generates the necessary artifacts and uses denylisting to ensure only authorized images are utilized.
The Release and Deliver Phase
Before software leaves the factory, a definitive go/no-go decision must be made. Anchore leverages its policy-as-code engine to fully automate this release decision, ensuring that all images pass your organization’s required gates and contractual policies prior to delivery.
| Phase | Feature | Anchore Enterprise Role |
|---|---|---|
| Develop | Source Code Evaluation | Stop vulnerable builds via policy-as-code. |
| Build | Dependency Management | Generate comprehensive artifact SBOMs. |
| Build | Artifact Repository | Continuously scan repositories for risks. |
| Test | License Compliance | Enforce OSS usage policies with policy-as-code. |
| Test | Container Security | Harden containers & manage exceptions. |
| Test | Container Policy Enforcement | Enforce STIG/NIST compliance with policy-as-code. |
| Release and Deliver | Release go/no-go decision | Automatego/no-go decision with policy-as-code. |
Production Operation Tools and Activities – Section 4.3
Once software moves beyond the factory, maintaining visibility and security in production environments is just as critical.
The Deploy Phase
During deployment, Anchore ensures smooth and secure delivery of containers to the registry. It generates the necessary SBOMs, vulnerability reports, and STIG outputs directly to an artifact repository and pushes the validated container to the applicable registry, providing these as artifacts to assessors. Once deployed, Anchore performs post-deployment security scans on running images using Kubernetes or Amazon ECS runtimes to continually check for vulnerabilities and compliance. You can also use application groups to monitor downstream releases over time and alert when new CVEs are discovered.
The Operate Phase
Continuous assessment is key in the Operate phase. Anchore provides a comprehensive supply chain security operations dashboard for this exact purpose. It continuously assesses and alerts on your Kubernetes container security posture. This maintains visibility over any container within the Anchore Enterprise SBOM inventory.
The Monitor Phase
Continuous monitoring forms the backbone of production security. Anchore facilitates Information Security Continuous Monitoring (ISCM). It actively detects security and compliance violations, generates findings, and provides actionable recommendations. It also offers comprehensive alerting and notification capabilities. Security personnel are immediately notified about policy violations and new CVEs across containers, open source code, and imported SBOMs. Finally, Anchore helps maintain an accurate asset inventory. It utilizes Kubernetes runtime inventory to monitor all deployed images across your clusters.
| Phase | Feature | Anchore Enterprise Role |
|---|---|---|
| Deploy | Deliver Containers | Push validated images & artifacts to registries. |
| Deploy | Post-Deployment Scan | Scan running images (K8s/ECS). |
| Operate | Operations Dashboard | Assess continuous K8s security posture. |
| Monitor | Information Security Continuous Monitoring (ISCM) | Detect violations & generate findings. |
| Monitor | Alerting and Notification | Notify on new CVEs & policy violations. |
| Monitor | Asset Inventory | Track deployed images via Kubernetes runtime inventory. |
Next Steps: Securing Your Software Factory
Aligning your software factory with the DoD DevSecOps Reference Design doesn’t have to be a manual, spreadsheet-heavy burden. With the right automated guardrails, you can accelerate software delivery without compromising on federal security standards.
Here is how you can get started:
- Assess Your Current Pipeline: Identify existing gaps in your source code evaluation and container scanning processes.
- Implement Policy-as-Code: Define your security rules centrally so that non-compliant or vulnerable builds are stopped automatically.
- Deploy Automated Guardrails: Integrate continuous scanning directly into your tools to meet DoD Reference Design requirements.
Get in touch with the Anchore Federal Team to discuss how we can help secure your DevSecOps pipelines.